Overview
One of the most powerful features of DNS (Domain Name System) is the ability to forward queries to other DNS servers. This functionality, known as forwarding, allows your DNS server to delegate name resolution tasks to external or partner DNS servers when it cannot resolve a query from its own zones. Forwarding not only improves efficiency but also reduces the load on your internal DNS infrastructure.
There are two types of forwarding covered in this guide: regular forwarding, which offloads all external queries to a single designated forwarder, and conditional forwarding, which routes queries for specific domain names to specific DNS servers – enabling fine-grained control over how name resolution is delegated.
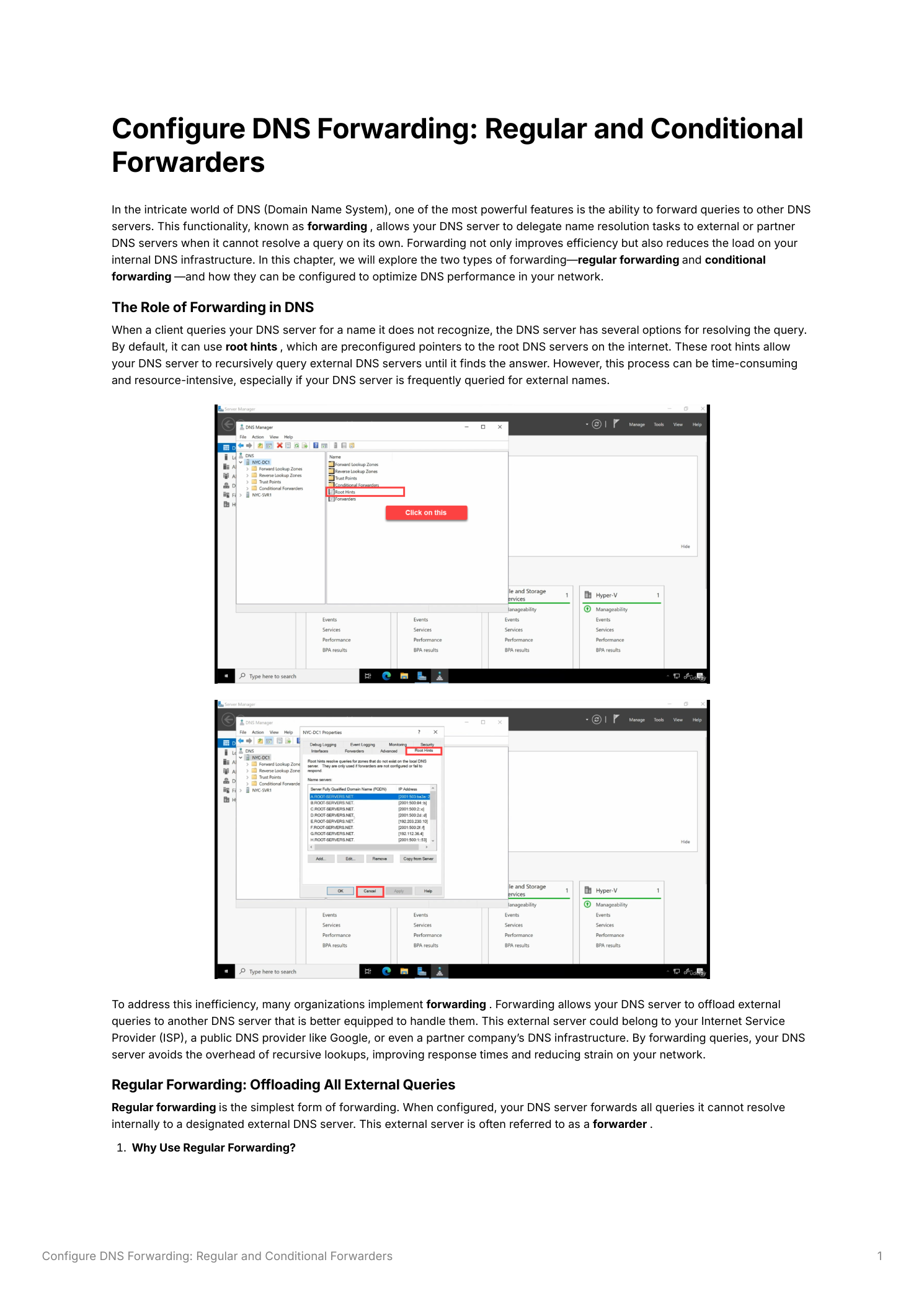
The Role of Forwarding in DNS
When a client queries your DNS server for a name it cannot resolve, the server has several options. By default, it can use recursive lookup – querying the DNS root servers and working down the hierarchy until it finds an authoritative answer. This process is reliable but time-consuming and resource-intensive, especially when your server is frequently queried for external names.
Forwarding replaces this recursive process with a simpler delegation: your DNS server passes the query to another, more capable DNS server – the forwarder – and waits for the answer. The forwarder resolves the query (using its own cache or recursion) and returns the result. Your server then relays the answer to the client.
Part 1 – Regular Forwarding
Regular forwarding is the simpler of the two types. When configured, your DNS server forwards all queries it cannot resolve from its internal zones to a designated external DNS server.
Why Use Regular Forwarding
- Efficiency – Forwarding external queries to a dedicated DNS server reduces the recursive workload on your internal DNS infrastructure
- Performance – Public DNS servers like Google’s
8.8.8.8or Cloudflare’s1.1.1.1are optimized for speed and reliability, with massive caches that return answers faster than a fresh recursive lookup - Security – By limiting direct access to root hints, you reduce the risk of your internal DNS server being exposed to DNS-based attacks from the internet
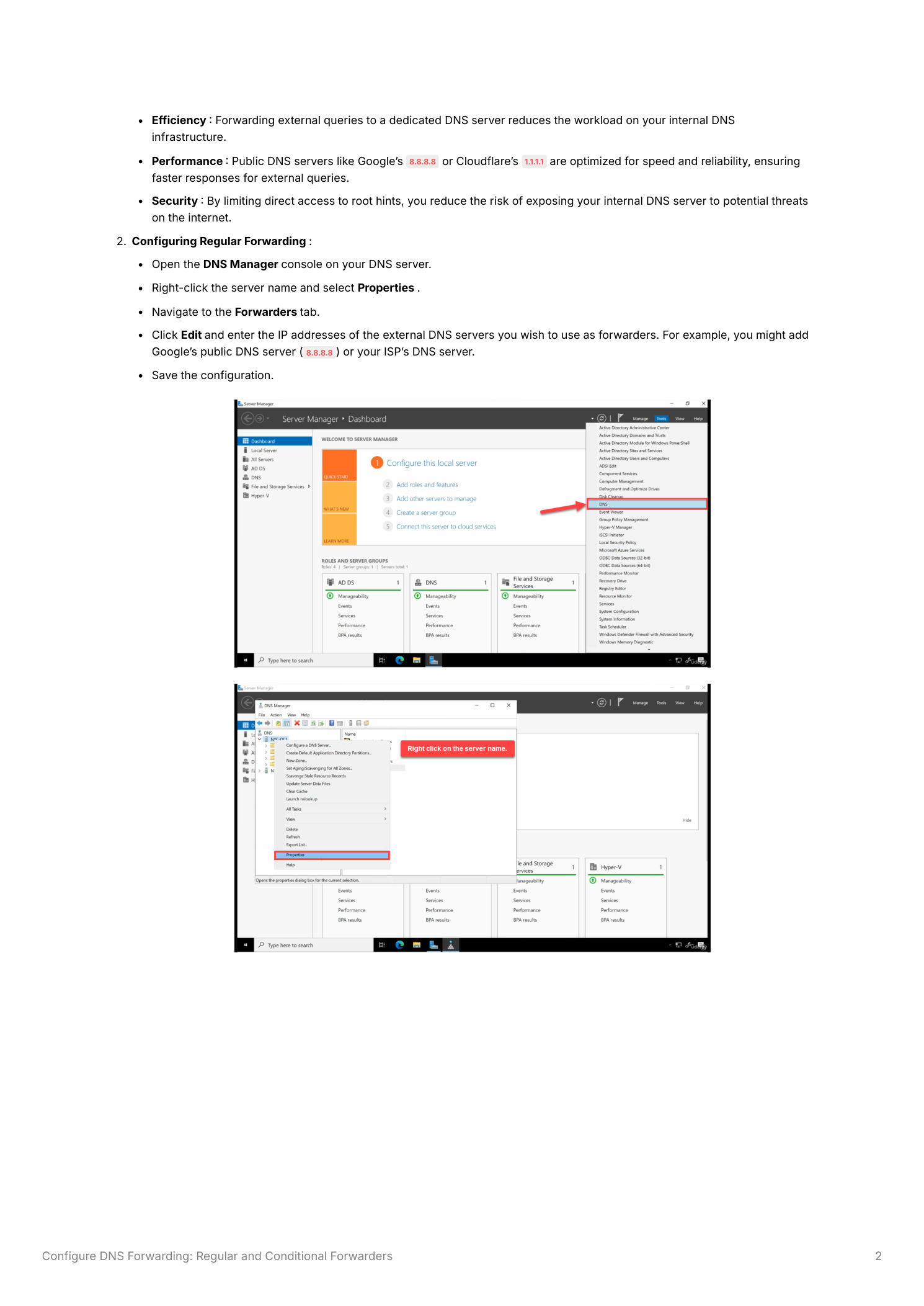
Configuring Regular Forwarding
- Open the DNS Manager console on your DNS server (Server Manager → Tools → DNS)
- Right-click the server name in the left panel and select Properties
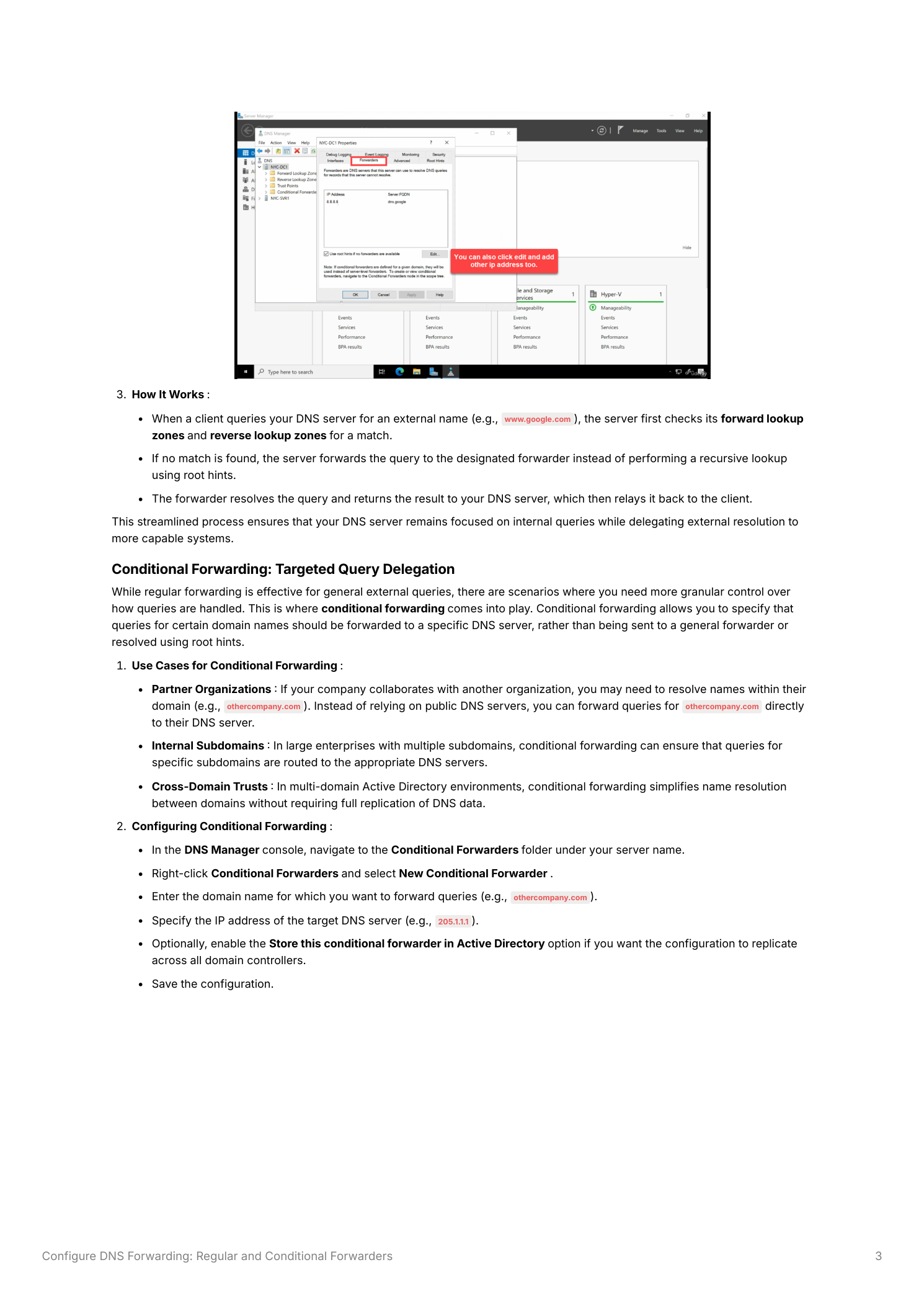
- Navigate to the Forwarders tab
- Click Edit and enter the IP addresses of the DNS servers you want to use as forwarders – for example,
8.8.8.8(Google) and8.8.4.4, or your ISP’s DNS servers - Click OK to save the configuration
How Regular Forwarding Works
When a client queries your DNS server for an external name (for example, www.microsoft.com), the server first checks its forward and reverse lookup zones for a match. If no match is found in the local zones, the query is forwarded to the designated forwarder. The forwarder resolves the name – using its own cache or performing recursion – and returns the answer to your DNS server, which relays it back to the client. This streamlined flow keeps your DNS server focused on internal queries while delegating external resolution to a more capable system.
Part 2 – Conditional Forwarding
While regular forwarding handles all external queries uniformly, there are scenarios where you need more granular control. Conditional forwarding allows you to specify that queries for a particular domain name should be forwarded to a specific DNS server, rather than to the general forwarder.
Use Cases for Conditional Forwarding
- Partner Organizations – If your company collaborates with another organization and needs to resolve names within their domain (for example,
partnercompany.com), you can forward those queries directly to the partner’s internal DNS server instead of relying on public DNS - Internal Subdomains – In large enterprises with multiple subdomains managed by different DNS servers, conditional forwarding ensures queries for specific subdomains go directly to the authoritative server for that zone
- Cross-Domain Trusts – In multi-domain Active Directory environments, conditional forwarding simplifies name resolution between domains without requiring full DNS zone replication or delegation
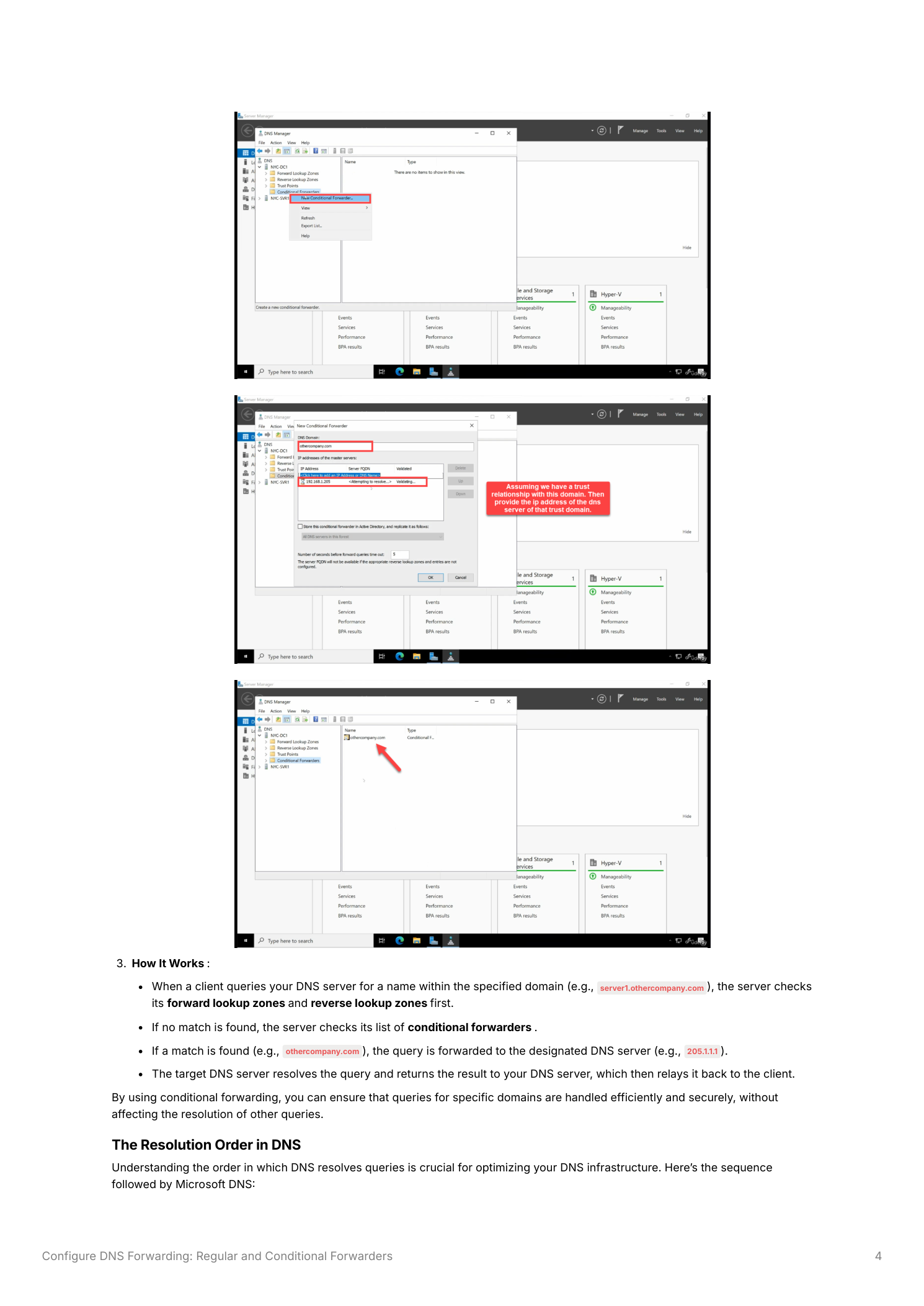
Configuring Conditional Forwarding
- In DNS Manager, expand the server node in the left panel and click Conditional Forwarders
- Right-click Conditional Forwarders and select New Conditional Forwarder
- Enter the DNS Domain name for which queries should be forwarded – for example,
partnercompany.com - Enter the IP address of the target DNS server that is authoritative for that domain – for example,
192.168.1.1 - Optionally, enable Store this conditional forwarder in Active Directory to replicate the configuration to all domain controllers in your domain automatically
- Click OK to save
How Conditional Forwarding Works
When a client queries your DNS server for a name within a conditionally forwarded domain (for example, server.partnercompany.com), the server checks its internal zones first. If no match is found locally, it checks the conditional forwarder list. Finding a match for partnercompany.com, it forwards the query directly to the configured target DNS server (e.g., 192.168.1.1). That server resolves the query and returns the answer, which your DNS server relays to the client. Queries for all other domains continue through the regular forwarder or root hints as normal.
DNS Resolution Order
Understanding the order in which Windows DNS resolves queries is critical for designing an effective forwarding strategy. Microsoft DNS resolves queries in the following sequence:
- Forward and Reverse Lookup Zones – The DNS server checks its local zone database first. If the name is authoritative in a hosted zone, it returns the answer immediately without forwarding
- Conditional Forwarders – If no local zone match is found, the server checks whether any conditional forwarder matches the queried domain. If a match exists, the query is forwarded to that specific server
- Regular Forwarders – If no conditional forwarder matches, the query is sent to the general forwarder configured in the Forwarders tab
- Root Hints – As a last resort (if no forwarders are configured, or if all forwarders fail to respond), the server falls back to recursive lookup using the root hints – querying the DNS root servers directly
This hierarchical resolution ensures that internal names are always resolved locally, partner or special-purpose domains are routed to the correct servers, and all remaining external queries flow through your designated forwarder rather than burdening your server with full recursion.
Practical Considerations
Choosing Forwarders Wisely
For regular forwarding, select reliable and fast DNS servers. Google Public DNS (8.8.8.8 / 8.8.4.4) and Cloudflare DNS (1.1.1.1 / 1.0.0.1) are popular choices with strong uptime records and global anycast infrastructure. You may also use your ISP’s DNS servers if your organization has a support relationship with them. For conditional forwarding, ensure the target DNS server is the actual authoritative server for the specified domain – misconfigured targets result in resolution failures for the affected domain.
Avoiding Over-Reliance on External Servers
While forwarding improves efficiency, your DNS infrastructure should not have a single point of failure. Configure at least two forwarder IP addresses in the Forwarders tab so that if the primary forwarder is unreachable, queries fall through to the secondary. Ensure root hints remain configured as a fallback – if all forwarders fail, Windows DNS can still resolve external names through recursion, preventing a complete DNS outage.
Active Directory Replication for Conditional Forwarders
When you enable Store this conditional forwarder in Active Directory, the conditional forwarder configuration is stored in the AD forest and replicated automatically to all domain controllers running the DNS Server role. This is the recommended approach in any multi-DC environment – it eliminates the need to manually configure the same conditional forwarder on every domain controller and ensures consistency across your DNS infrastructure as DCs are added or removed.
