Overview
File screening is a Windows Server feature built into the File Server Resource Manager (FSRM) role that controls which file types can be saved to specific folders. A file screen applies a set of rules to a folder path and either actively blocks unauthorized file types from being written or passively monitors and logs them without blocking. Common use cases include preventing users from storing media files (.mp3, .avi) or executable files (.exe, .bat) in shared business folders, helping organizations enforce data governance policies and reduce unnecessary storage consumption.
This guide covers the complete FSRM file screening workflow: installing the FSRM role, opening the FSRM console, understanding the three key concepts (File Screens, File Screen Templates, and File Groups), creating a reusable File Screen Template with Active screening and event log notification, applying a File Screen to a specific folder, testing the block behavior, and modifying or deleting a file screen after it is in place.
Step 1 – Install File Server Resource Manager (FSRM)
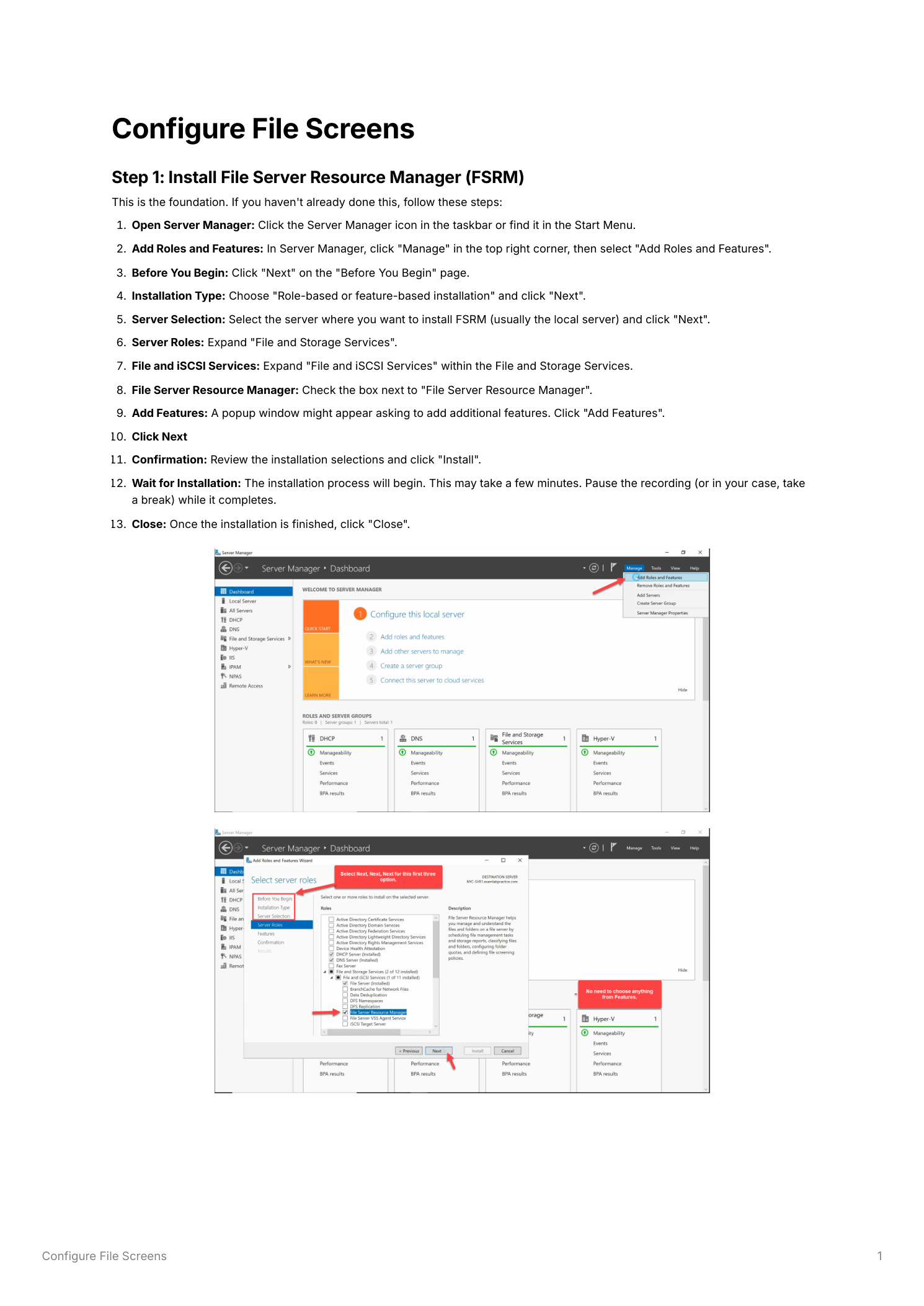
Open Server Manager from the taskbar or Start menu. In the top-right corner of the Server Manager dashboard, click Manage and select Add Roles and Features. On the Before You Begin page, click Next. Select Role-based or feature-based installation and click Next. On the Server Selection page, select the local server and click Next.
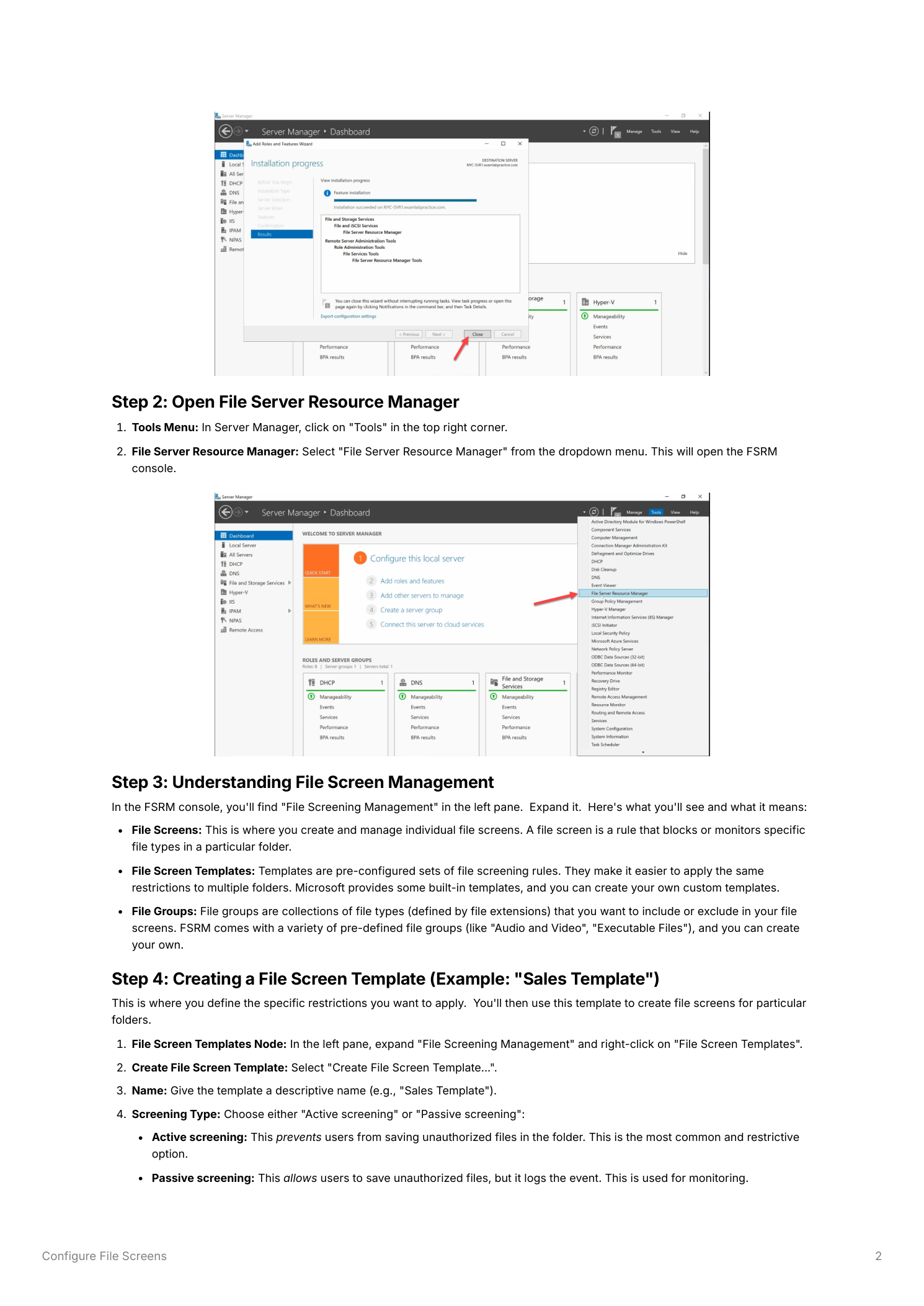
On the Server Roles page, expand File and iSCSI Services within the File and Storage Services group. Check File Server Resource Manager. A dialog prompts you to add required management tools – click Add Features. Click Next through the Features page (no additional features are needed), then click Next and Install on the Confirmation page. The installation takes a few minutes. Click Close when it finishes.
Step 2 – Open the FSRM Console
After installation, open the FSRM management console from Server Manager → Tools → File Server Resource Manager. The console opens with a tree view in the left pane organized into major feature areas. Expand File Screening Management to reveal the three nodes you will use throughout this guide: File Screens, File Screen Templates, and File Groups.
Step 3 – Understanding the Three Key Concepts
Before creating a file screen, it helps to understand how FSRM organizes file screening into three layers:
- File Groups – Collections of file types defined by extension patterns. FSRM ships with built-in groups such as “Audio and Video Files” (.mp3, .avi, .wmv, .wav, .mov) and “Executable Files” (.exe, .bat, .cmd, .msi). You can create custom groups for any file type pattern your environment requires
- File Screen Templates – Pre-configured, reusable sets of screening rules. A template defines the screening type (Active or Passive), which File Groups to restrict, and which notifications to trigger. Templates make it easy to apply consistent rules across many folders without rebuilding the configuration each time
- File Screens – The actual enforcement objects. A File Screen applies a template (or custom settings) to a specific folder path. All files saved to that folder are evaluated against the template’s File Groups and screening type
Step 4 – Create a File Screen Template
In the FSRM console, right-click File Screen Templates and select Create File Screen Template. In the dialog that opens, configure the following on the Settings tab:
- Template Name – Enter a descriptive name such as “Sales Template”
- Screening Type – Select Active screening to prevent unauthorized files from being saved. Active screening is the most restrictive option. Alternatively, Passive screening allows the save but logs an event, useful for monitoring without disruption during initial rollout
- File Groups – In the “File groups” section, check the groups whose file types you want to block or monitor. For a business shared folder, typical selections include “Audio and Video Files” and “Executable Files”
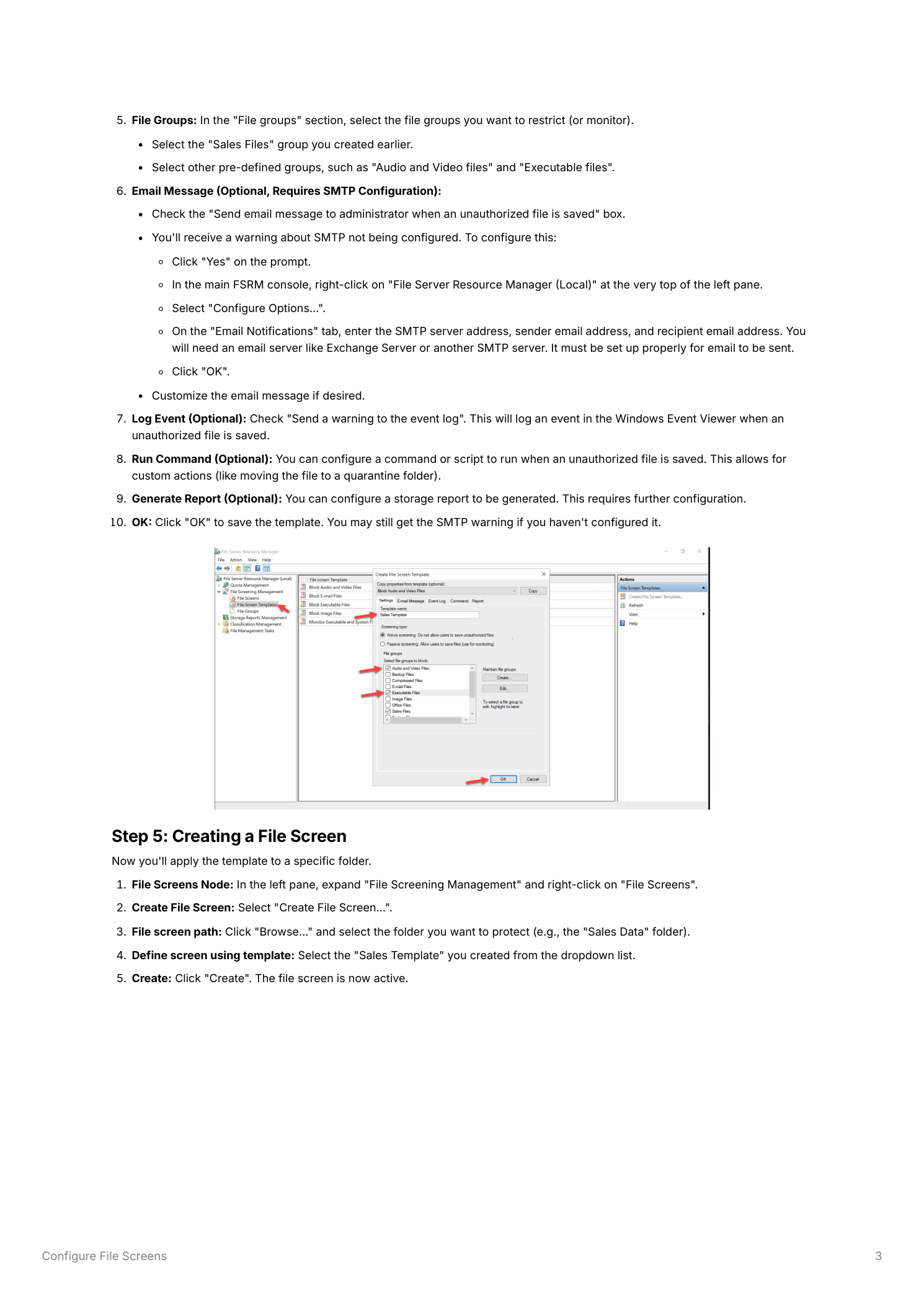
Optionally configure the additional notification tabs:
- Email Message – Check “Send email to administrator when an unauthorized file is saved” and configure your SMTP server settings in FSRM’s global options to enable email delivery
- Event Log – Check “Send a warning to the event log” to write an event to the Windows Event Viewer each time a violation occurs. This is useful for auditing without requiring email infrastructure
- Run Command – Optionally specify a script or program to run when a violation occurs, such as moving the file to a quarantine location
- Generate Report – Optionally generate a storage report on violation events
Click OK to save the template. It appears in the File Screen Templates node and is now available to apply to any folder.
Step 5 – Create a File Screen
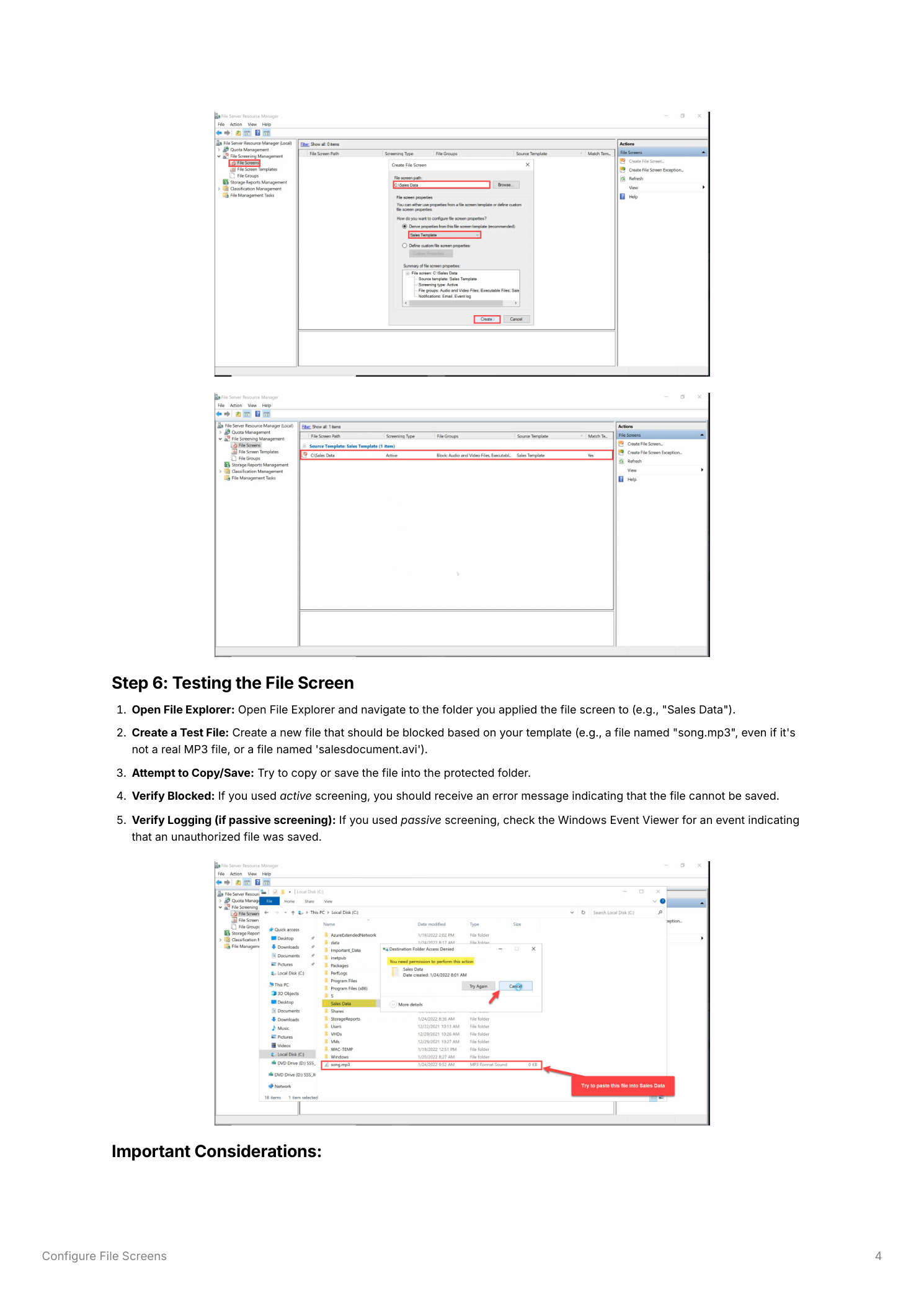
In the FSRM console, right-click File Screens and select Create File Screen. On the Create File Screen dialog:
- File screen path – Click Browse and select the folder you want to protect, such as a shared “Sales Data” folder
- Define screen – Select “Derive properties from this file screen template” and choose the template you just created from the dropdown list
- Click Create
The file screen appears immediately in the File Screens node in the console, showing the folder path and the template applied. The screen is active – any attempt to save a restricted file type to that folder will now be blocked (Active screening) or logged (Passive screening).
Step 6 – Test the File Screen
To verify the file screen is working correctly:
- Open File Explorer and navigate to the folder where you applied the file screen
- Attempt to create or copy a file that matches a blocked type – for example, a file named “song.mp3” or “test.exe”
- With Active screening, you will receive an error message indicating that the file cannot be saved to that location
- With Passive screening, the save completes normally but an event is written to the Windows Event Viewer under Windows Logs → Application
Step 7 – Modify a File Screen
File screens and templates can be updated at any time without recreating them from scratch:
- Edit file screen properties – In the FSRM console under File Screens, right-click the file screen entry and select Edit File Screen Properties. This opens the same configuration dialog used at creation. You can change the screening type, switch templates, or override specific settings on a per-folder basis by selecting “Define custom file screen properties”
- Edit the template – If the same template is applied to multiple folders, editing the template propagates the change to all file screens that use it. Right-click the template in File Screen Templates and select Edit Template Properties. After making changes, choose to update all derived file screens when prompted
Step 8 – Delete a File Screen
To remove a file screen from a folder without deleting the template, right-click the file screen entry in the File Screens node and select Delete File Screen. Confirm the deletion. The folder is immediately no longer subject to screening – files of any type can be saved without restriction. The template itself remains in File Screen Templates and can be reapplied to any folder at any time.
Best Practices
- Start with Passive Screening – Deploy new file screens in Passive mode first to identify which users and applications would be affected before switching to Active blocking. This avoids surprise disruptions to workflows that legitimately use restricted file types
- Communicate with Users – Inform users about file screening policies before enabling Active screening so they understand why saves may be blocked. This reduces support calls and frustration
- Configure SMTP for Notifications – Set up SMTP server details in FSRM’s global options (Action → Configure Options → Email Notifications tab) before enabling email alerts. Without SMTP configured, email notifications are silently dropped
- Use Templates for Consistency – Apply the same template to all similarly-purposed shared folders rather than creating custom per-folder screens. Changes to the template then propagate consistently across the entire environment
- Review File Groups Before Blocking – Verify that the selected File Groups do not include extensions used by legitimate business applications in that folder. Blocking the wrong extension can break application workflows in ways that are difficult to diagnose
- Audit Regularly – Review Event Viewer and FSRM reports periodically to ensure screening policies remain aligned with current business requirements and that no legitimate use cases are being unintentionally blocked
