Overview
In large organizations, managing IP addresses across multiple locations, subnets, and even continents becomes exponentially complex as the network grows. Without a centralized system, IT teams resort to spreadsheets and manual processes to track IP allocations – an approach that is error-prone and difficult to maintain, especially in dynamic environments where IP assignments change frequently. IP Address Management (IPAM) is a feature introduced by Microsoft to provide a unified platform for monitoring, managing, and auditing IP address usage across an entire organization’s DHCP servers, DNS servers, and domain controllers.
IPAM integrates seamlessly with DHCP, DNS, and other network services, offering real-time visibility into IP allocations and automating administrative tasks such as scope utilization monitoring and server discovery.
The Problem IPAM Solves
Consider an organization with multiple geographic locations, each hosting its own DHCP servers, DNS servers, and domain controllers. As the network grows, questions arise: which IP addresses are currently in use? Are there conflicts or duplicate assignments? How can administrators efficiently allocate new addresses without disrupting existing services? Without a centralized tool, these tasks become overwhelming. IPAM addresses these challenges by providing a single console that aggregates data from all managed network services.
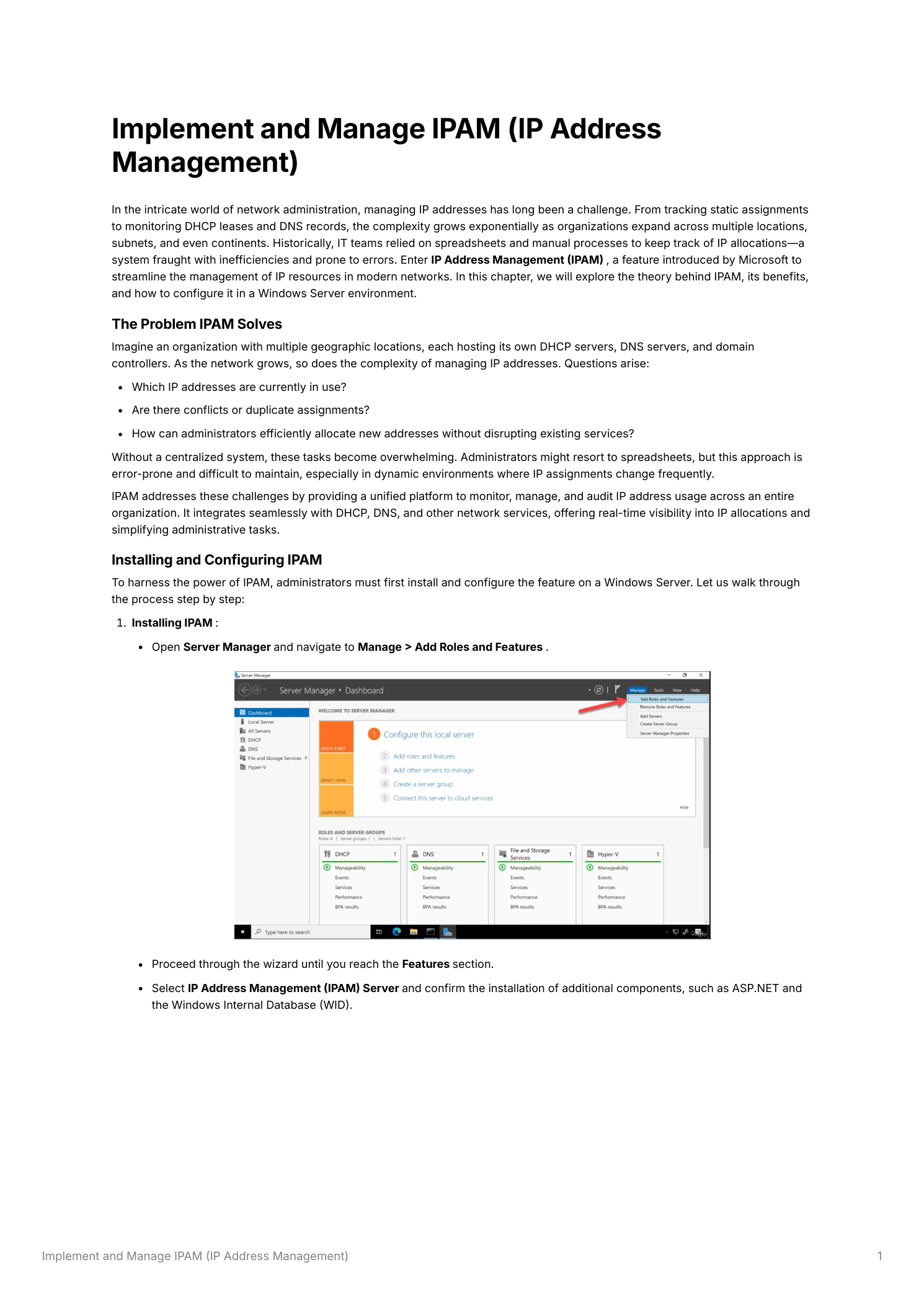
Step 1 – Install the IPAM Feature
Open Server Manager and navigate to Manage → Add Roles and Features. Proceed through the wizard until you reach the Features section. Locate and select IP Address Management (IPAM) Server. The wizard will automatically include required dependencies – confirm the addition of ASP.NET components and the Windows Internal Database (WID), which IPAM uses as its local data store. Click Install and complete the installation.
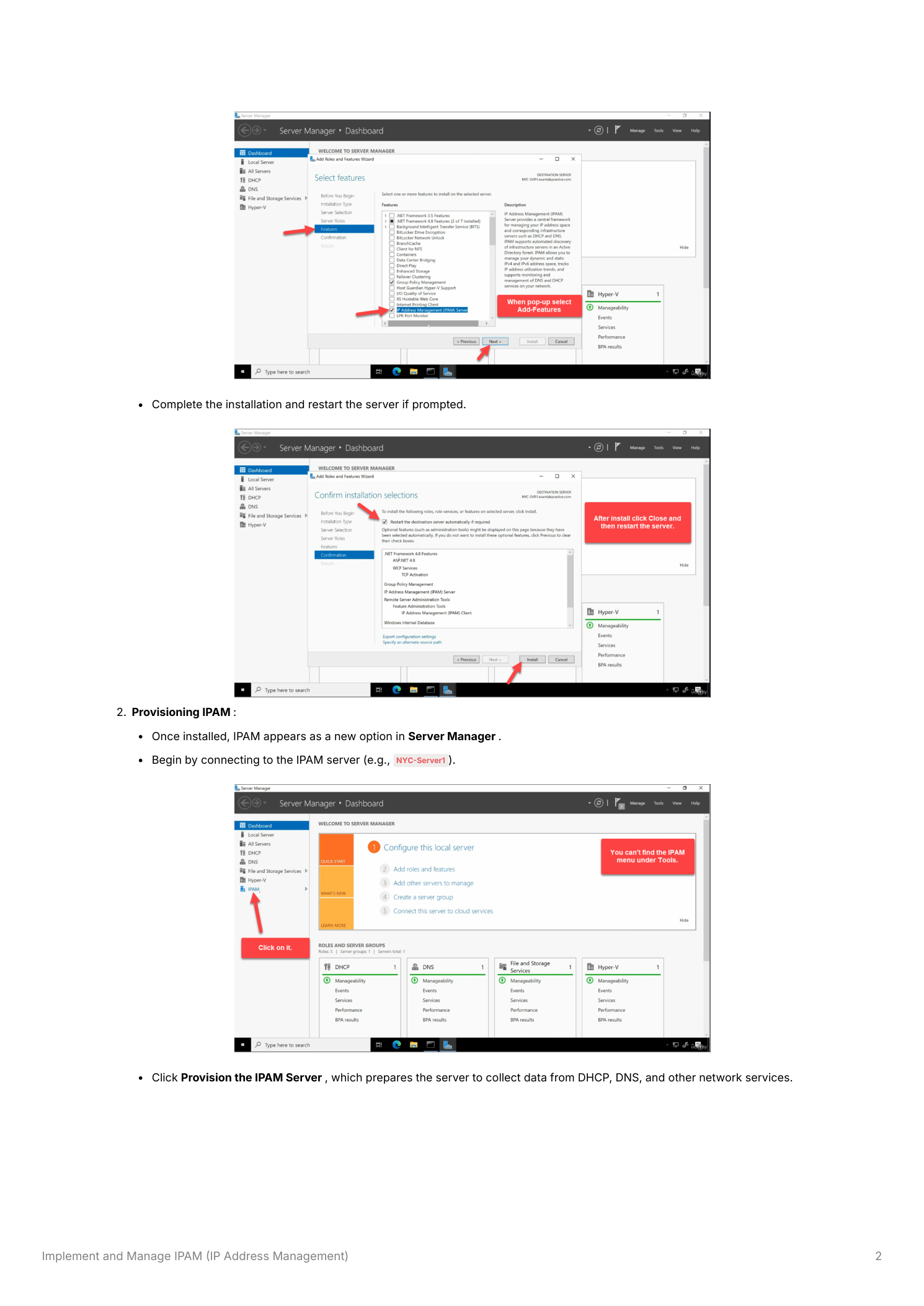
Step 2 – Provision the IPAM Server
Once installed, click IPAM in Server Manager’s left panel to open the IPAM console. The console will display a task list guiding you through the initial setup. The first task is to connect to the IPAM server – click it to establish the connection. Next, click Provision the IPAM Server. This step prepares IPAM to collect data from DHCP, DNS, and other network services by setting up the required database schema and communication infrastructure.
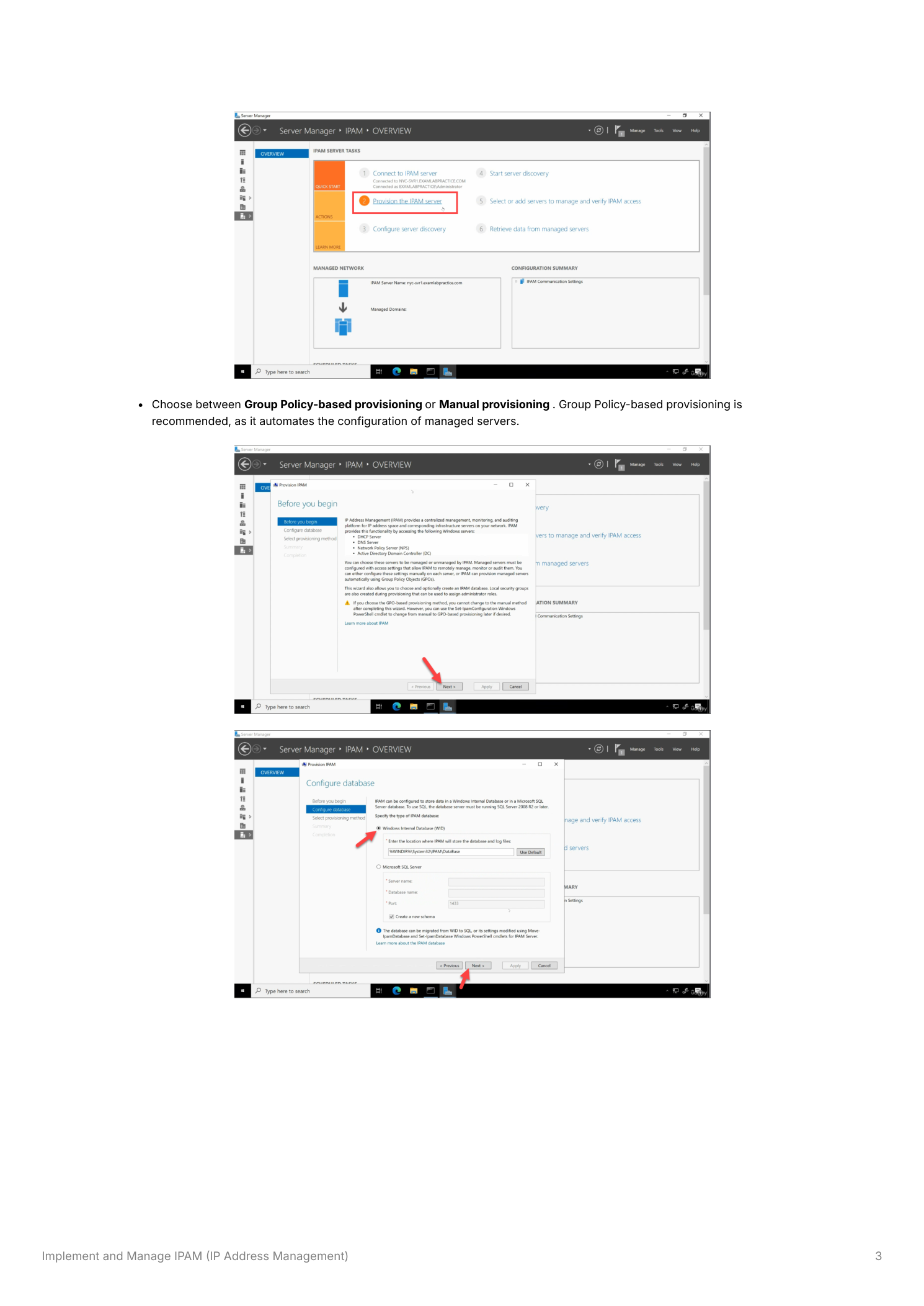
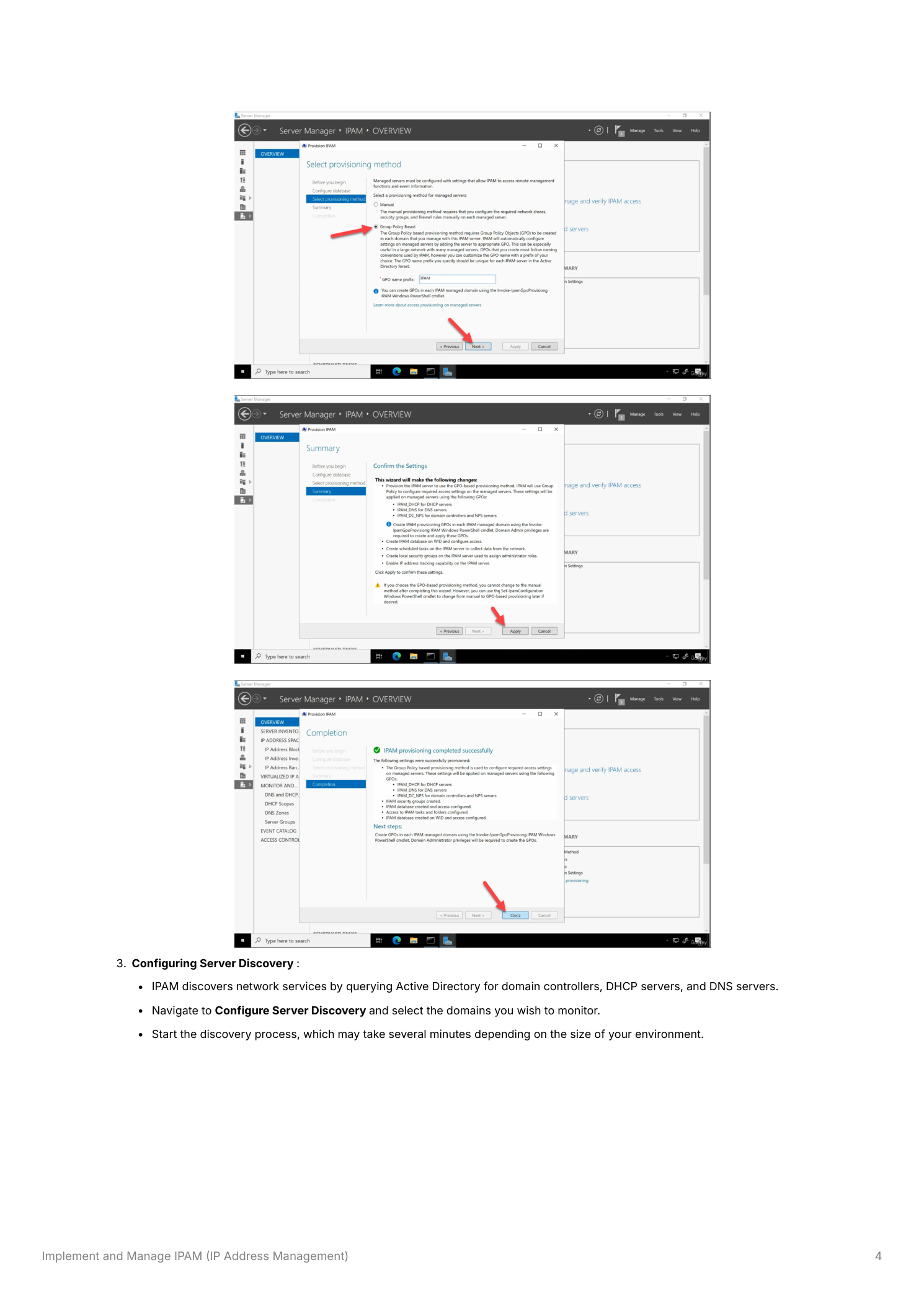
When prompted to select a provisioning method, choose Group Policy-based provisioning. This is the recommended approach – it automatically creates and applies Group Policy Objects to configure the managed DHCP, DNS, and domain controller servers, eliminating the need for manual firewall rule and access configuration on each server. Enter a GPO name prefix (for example, IPAM) when prompted – this prefix is used to name the three GPOs that IPAM creates.
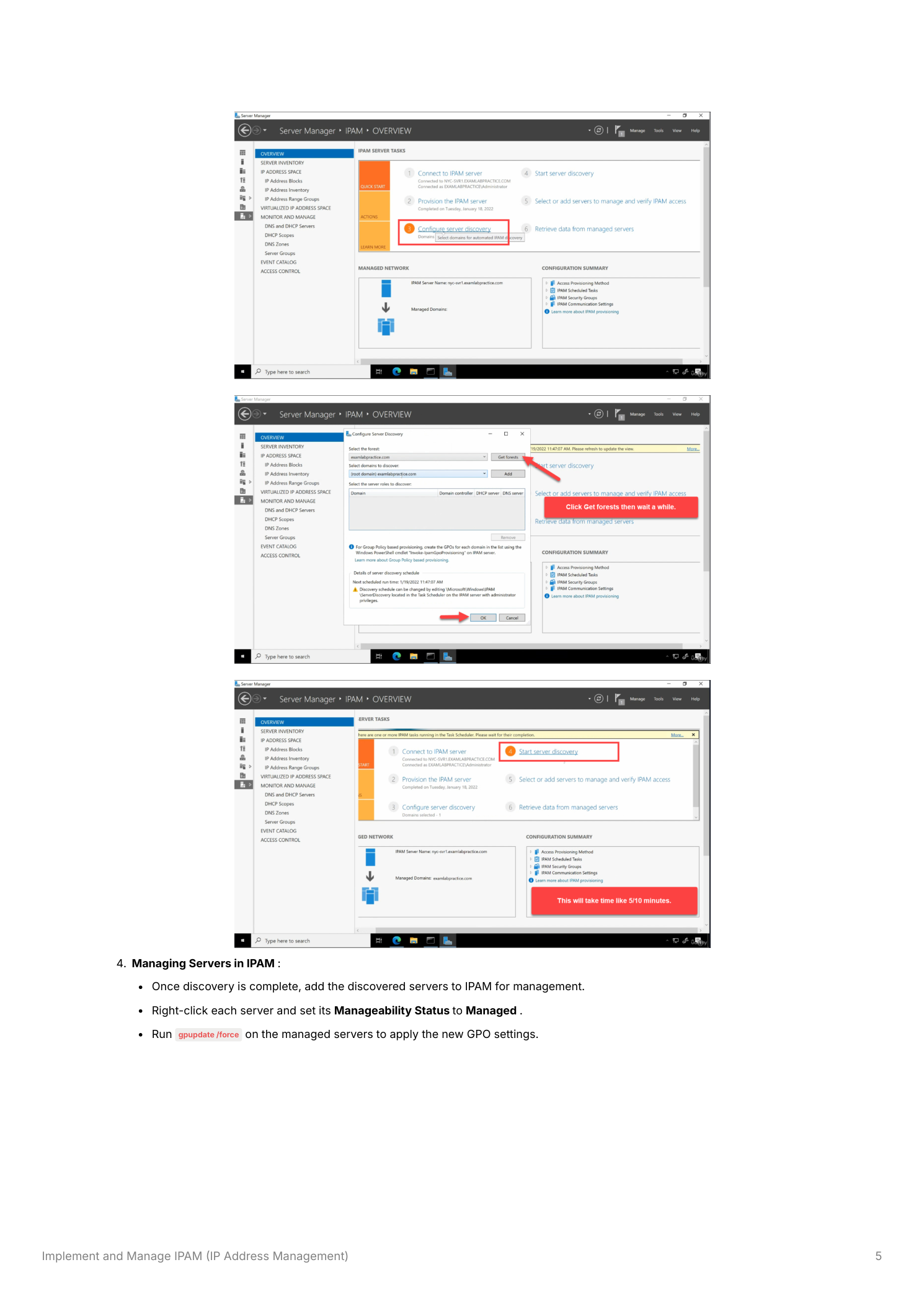
Step 3 – Configure Server Discovery
After provisioning, the next task is Configure Server Discovery. IPAM discovers your network infrastructure by querying Active Directory to locate domain controllers, DHCP servers, and DNS servers within the specified domains. Click Configure Server Discovery, add the domains you want IPAM to monitor, and click OK. Then click Start Server Discovery to begin the discovery process – this may take several minutes depending on the size of your environment.
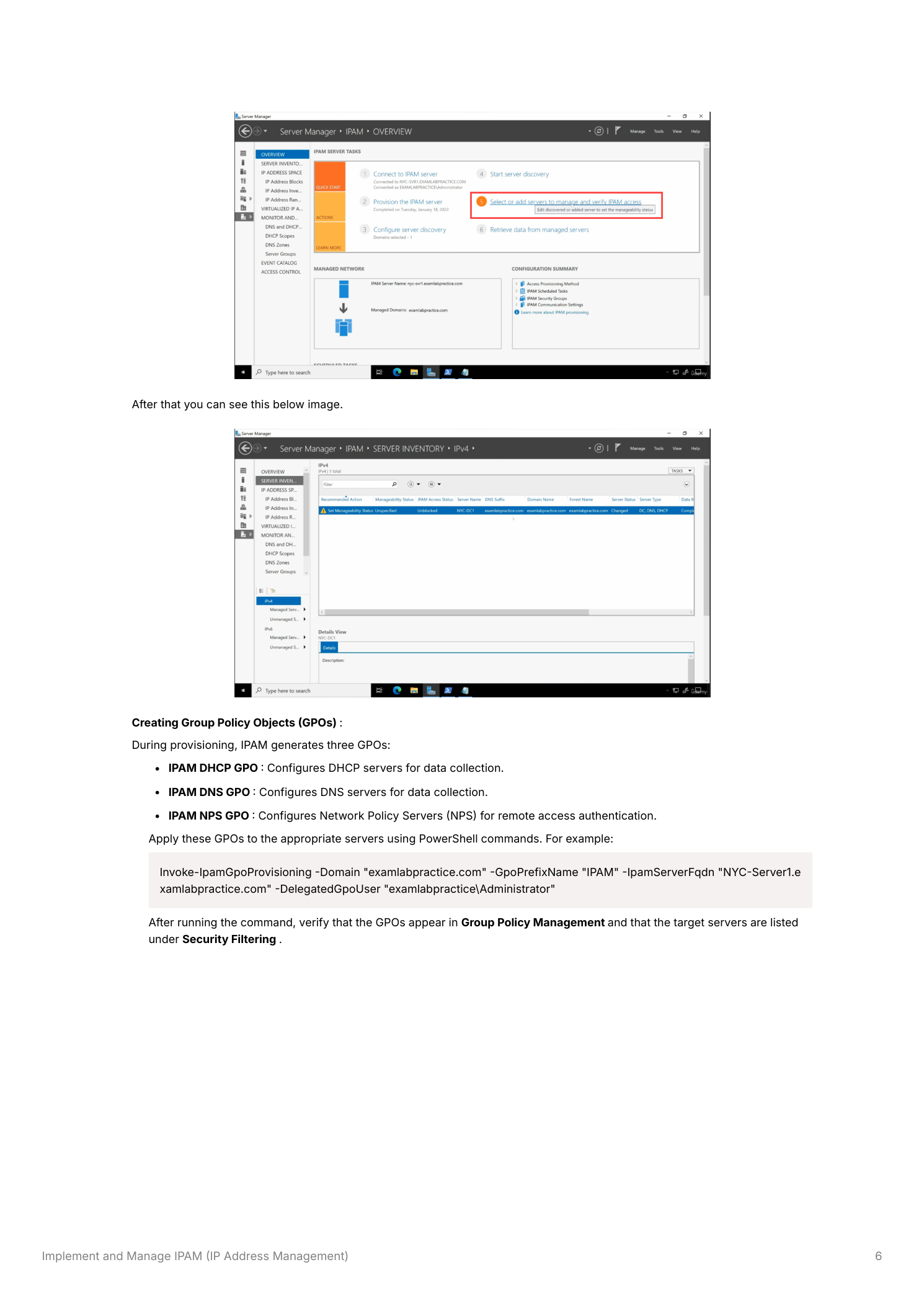
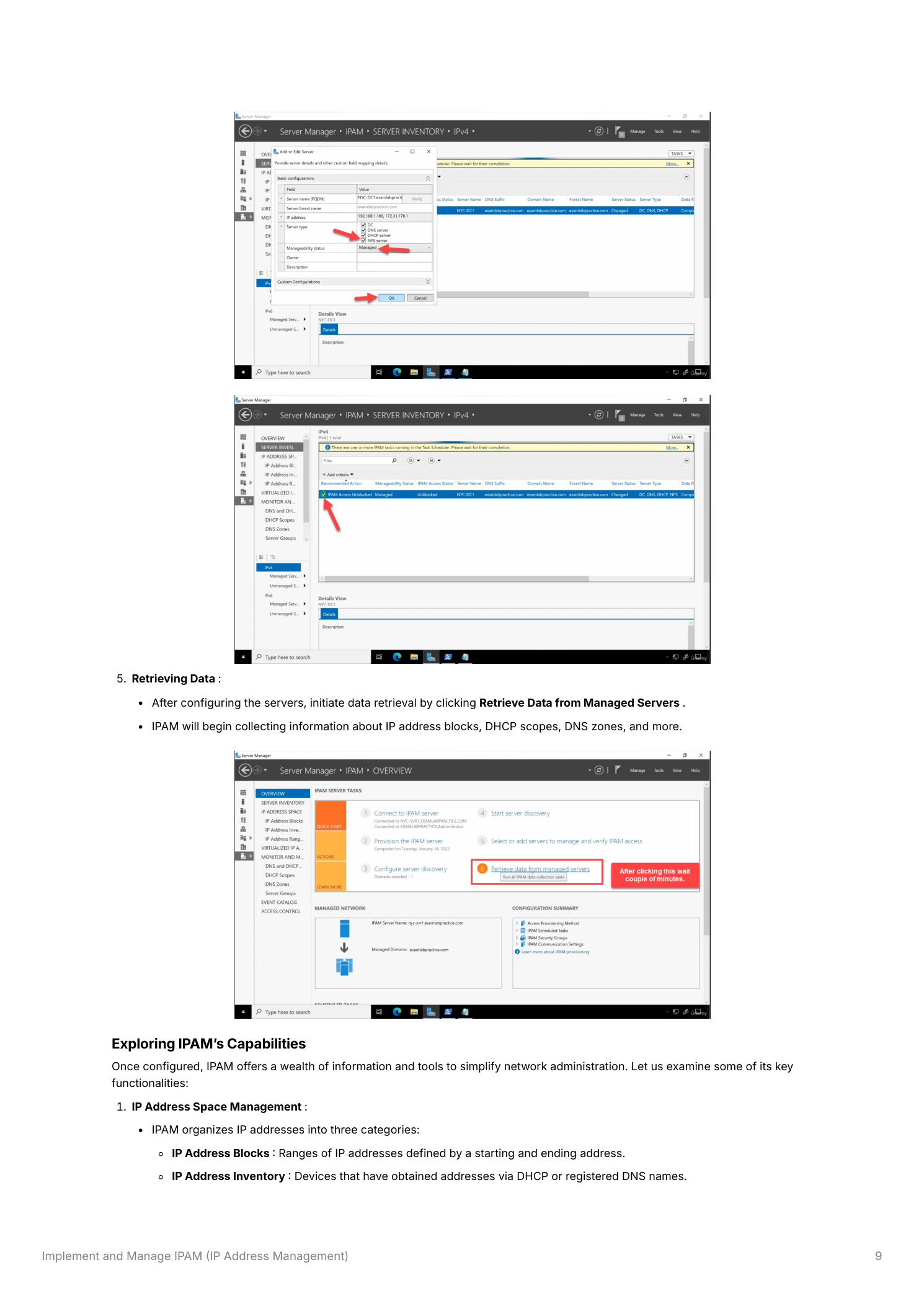
Step 4 – Manage Discovered Servers
Once server discovery completes, the discovered servers appear in the SERVER INVENTORY view. Each server will initially show a Manageability Status of Unspecified. Right-click each server you want IPAM to manage and set its Manageability Status to Managed. After setting all target servers to Managed, run gpupdate /force on each managed server to apply the IPAM GPO settings immediately.
Step 5 – Apply IPAM GPOs
During provisioning, IPAM generated three Group Policy Objects that must be linked to the appropriate OUs containing the managed servers:
- IPAM DHCP GPO – Configures DHCP servers to allow IPAM data collection (opens required firewall rules and grants IPAM access)
- IPAM DNS GPO – Configures DNS servers for IPAM data collection
- IPAM NPS GPO – Configures Network Policy Servers (NPS) for remote access authentication and IPAM integration
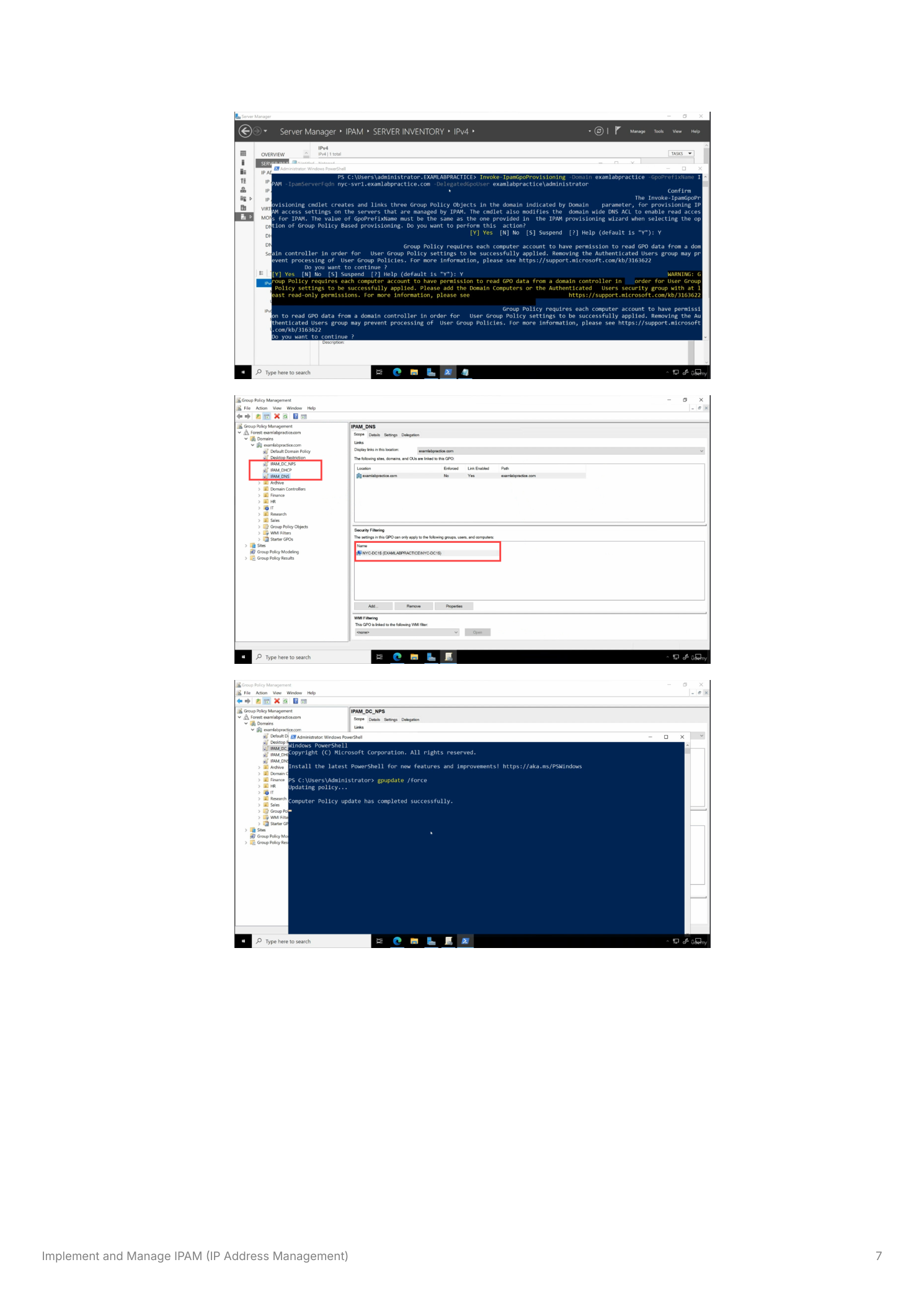
Apply these GPOs using the Invoke-IpamGpoProvisioning PowerShell cmdlet:
Invoke-IpamGpoProvisioning -Domain "yourdomain.com"
-GpoPrefixName "IPAM"
-IpamServerFqdn "YourIPAMServer.yourdomain.com"
-DelegatedGpoUser "yourdomain\Administrator"After running the command, open Group Policy Management to verify that the three IPAM GPOs are visible and that the target servers appear in the Security Filtering section of each GPO.
Step 6 – Verify Server Access Status
After applying the GPOs and running gpupdate on the managed servers, return to the IPAM SERVER INVENTORY view. Right-click each managed server and select Refresh Server Access Status. Once IPAM successfully communicates with a server, the IPAM Access Status column will change to Unblocked, confirming that IPAM can collect data from that server. If a server remains blocked, verify that the GPO has been applied (gpresult /r) and that required firewall ports are open.
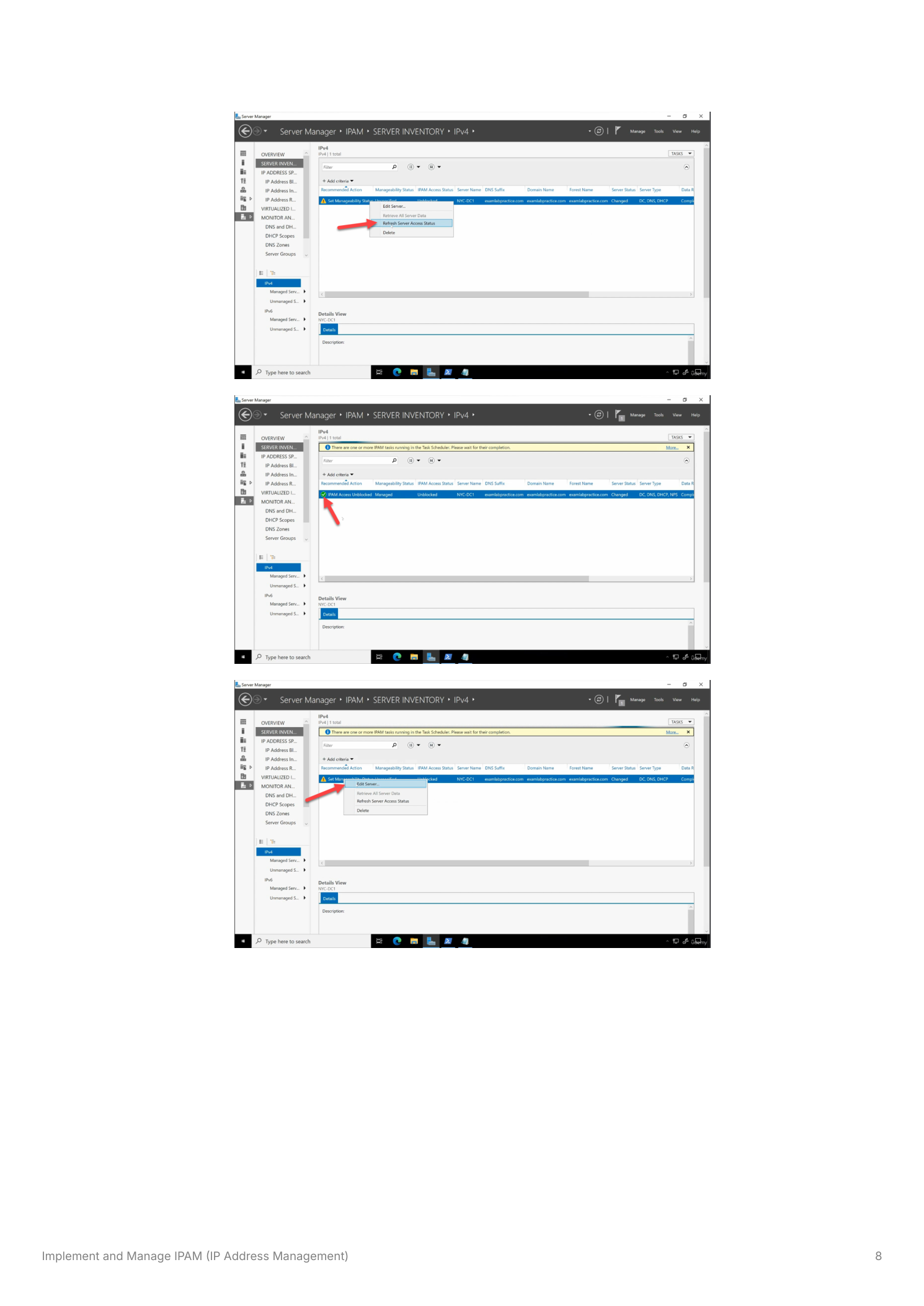
Step 7 – Retrieve Data from Managed Servers
With all servers showing Unblocked status, click Retrieve Data from Managed Servers in the IPAM task list. IPAM will query each managed server and populate its database with IP address blocks, DHCP scope configurations and utilization statistics, DNS zone information, and server inventory details. This initial data retrieval may take a few minutes. IPAM then continues to collect data automatically on a scheduled basis.
Exploring IPAM’s Capabilities
IP Address Space Management
IPAM organizes IP addresses into three tiers:
- IP Address Blocks – Top-level ranges defined by a starting and ending address (e.g.,
10.0.0.0/8) - IP Address Inventory – Individual addresses that have been assigned via DHCP or registered through DNS name records
- Range Groups – Logical groupings of IP address blocks, used to represent different physical locations or organizational departments
Administrators can manually add static IP ranges or modify existing ones directly from the IPAM console to reflect organizational changes – no need to connect to individual DHCP servers.
DHCP Scope Management
IPAM displays all DHCP scopes across all managed servers in a single view, including per-scope utilization statistics showing how many addresses are in use versus available. Administrators can edit scope properties – including the scope range, exclusions, and lease duration – directly from the IPAM console, with changes propagating to the target DHCP server automatically.
DNS Zone Monitoring
While IPAM does not import or manage individual DNS records (A, CNAME, MX, etc.), it provides visibility into DNS zone configurations and their associated IP address ranges. This functionality helps administrators ensure consistency between DNS zones and DHCP scopes – for example, confirming that a DNS zone’s associated subnet matches the DHCP scope serving that subnet.
Reporting and Auditing
IPAM generates detailed reports on IP address usage trends, DHCP lease activity, and DNS zone updates. These reports are valuable for capacity planning (identifying subnets approaching exhaustion), troubleshooting (correlating IP assignments with specific DHCP servers), and regulatory compliance (providing an auditable record of IP address assignments over time).
Limitations
Azure Integration – IPAM can track IP assignments for Azure virtual machines connected via VPN or ExpressRoute, but deeper native integration with Azure’s address management remains limited. Organizations with significant Azure footprints may need supplementary tools for cloud IP tracking.
DNS Record Association – IPAM does not pull individual DNS records into its database. It focuses on associating DNS zones with IP address ranges rather than providing a full DNS record management interface. Use DNS Manager or PowerShell for individual record management.
