Overview
DHCP (Dynamic Host Configuration Protocol) is one of the most foundational technologies in network administration, automating the process of assigning IP addresses to devices on a network. Without DHCP, administrators would need to manually configure every device – a tedious and error-prone task, especially in large networks. Windows Server, with its advanced DHCP capabilities, offers a centralized and scalable way to manage IP address allocation.
This guide covers installing the DHCP Server role, addressing the static IP prerequisite, completing the post-installation configuration wizard, authorizing the server in Active Directory, and configuring the DHCP console to begin issuing addresses. It also explores the critical concept of DHCP authorization – a feature unique to Microsoft Active Directory environments that prevents rogue DHCP servers from disrupting the network.
The Role of DHCP in Modern Networks
At its core, DHCP eliminates network administration overhead by dynamically assigning IP addresses to devices. Without it, administrators would need to manually configure each device – a tedious and error-prone task in large networks. DHCP eliminates this burden by automatically providing devices with the essential network parameters they need:
- IP Address – The unique identifier for the device on the network
- Subnet Mask – Defines the network boundaries and determines how traffic is routed
- Default Gateway – The router that facilitates communication between the local network and external networks, including the internet
- DNS Servers – Enables devices to resolve domain names into IP addresses
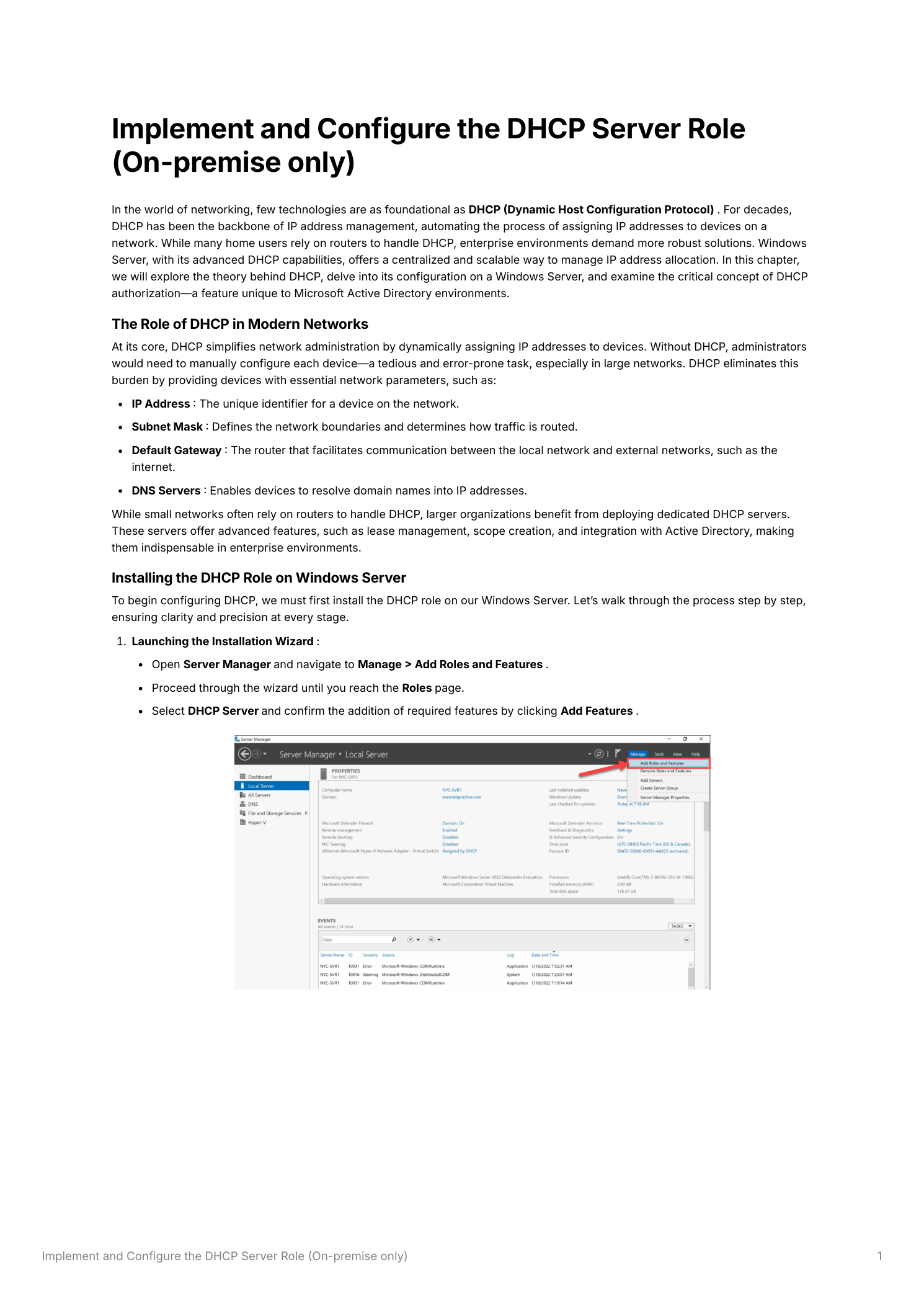
Step 1 – Install the DHCP Server Role
Open Server Manager and navigate to Manage → Add Roles and Features. Proceed through the wizard until you reach the Server Roles page. Locate and select DHCP Server. When prompted to add required features, click Add Features to confirm. Continue through the wizard and click Install.
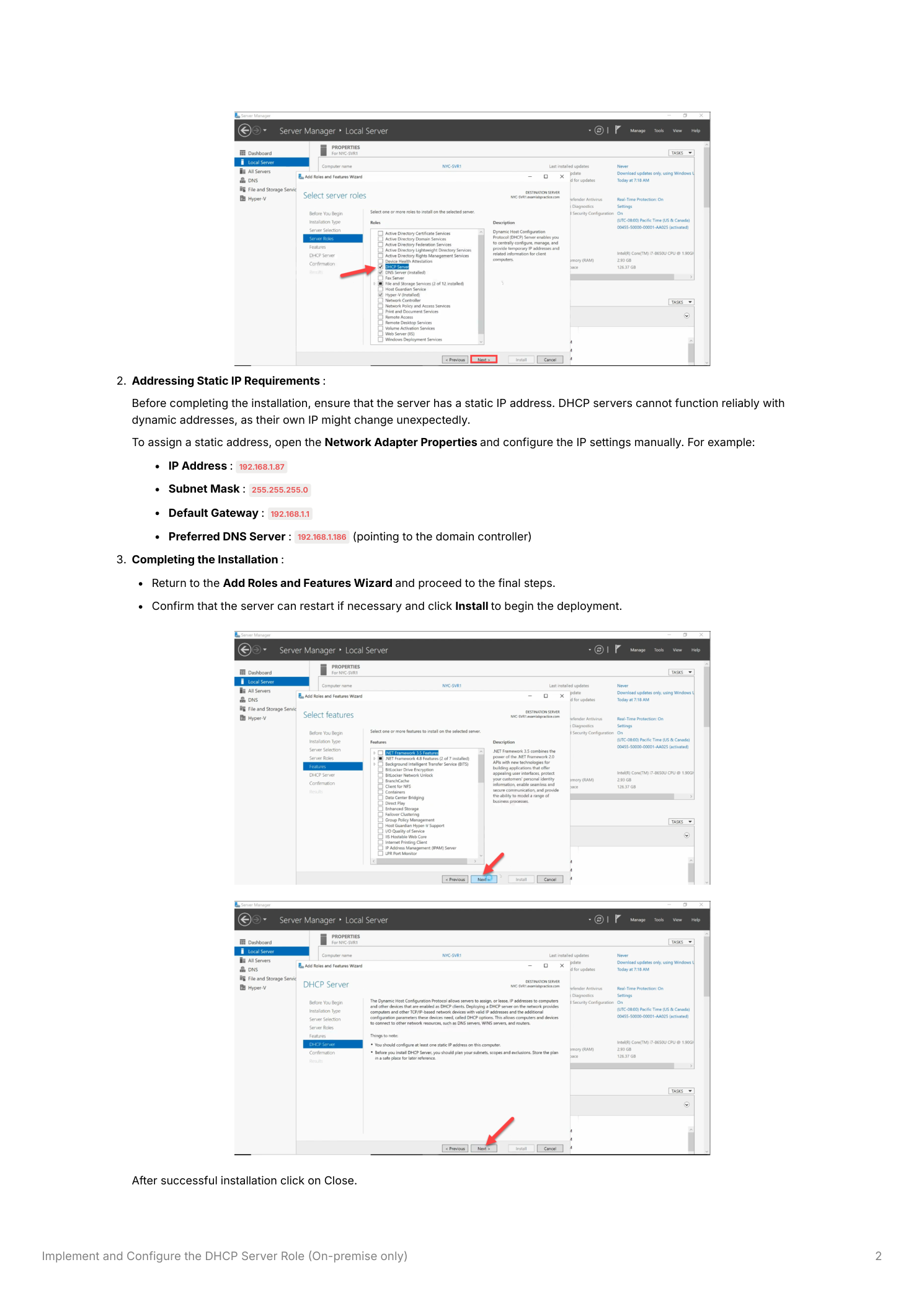
Step 2 – Assign a Static IP Address
Before completing the installation, ensure the server has a static IP address. DHCP servers cannot function reliably with dynamically assigned addresses – if the server’s own IP address changes, clients that have leases from this server will be unable to renew them. To assign a static IP, open Network Adapter Properties and configure the IPv4 settings manually. A typical configuration for a domain environment looks like this:
- IP Address:
192.168.1.10(or your chosen server address) - Subnet Mask:
255.255.255.0 - Default Gateway:
192.168.1.1 - Preferred DNS Server:
192.168.1.1(pointing to the domain controller)
After configuring the static IP, return to the Add Roles and Features Wizard, proceed to the final steps, and click Install. Restart the server if prompted, then click Close once installation completes.
Step 3 – Authorize the DHCP Server in Active Directory
After installation, the DHCP role appears in the Tools menu of Server Manager. However, before the server can begin issuing IP addresses, one critical step remains: DHCP authorization. In the DHCP console (Tools → DHCP), you will notice red downward arrows next to the IPv4 and IPv6 nodes – these indicate that the server is not yet authorized and cannot issue leases.
Additionally, a warning symbol appears in Server Manager’s notification area. Click the warning flag and select Complete DHCP Configuration to launch the DHCP Post-Installation Configuration Wizard.
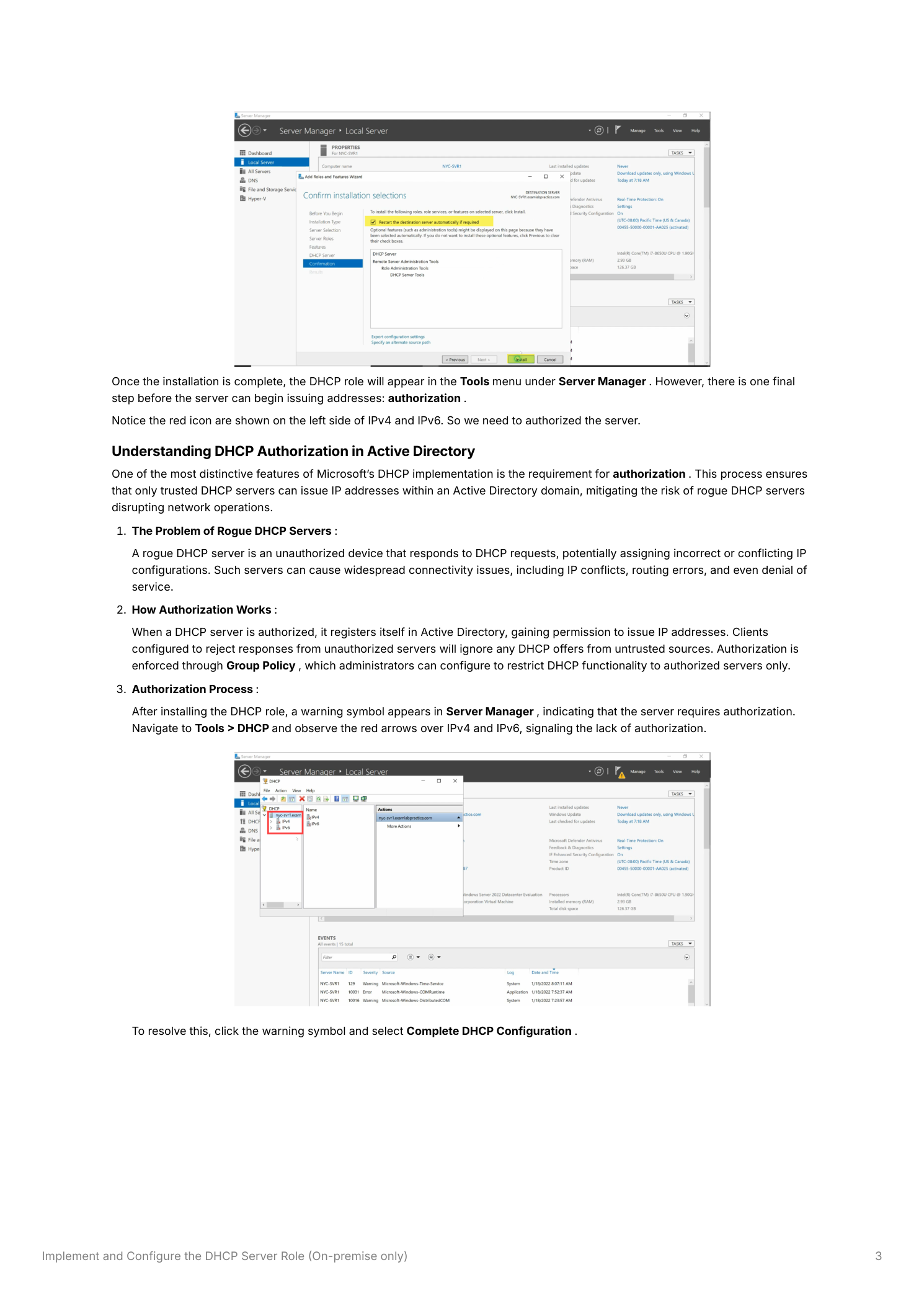
Why Authorization Matters
DHCP authorization is a safeguard built into Microsoft Active Directory to prevent rogue DHCP servers – unauthorized servers that respond to DHCP requests and potentially assign incorrect IP configurations, causing IP conflicts, routing failures, or even a complete network outage. When a DHCP server is authorized, it registers itself in Active Directory. Clients on the domain are configured (via Group Policy) to accept DHCP offers only from authorized servers, blocking responses from any unrecognized DHCP server.
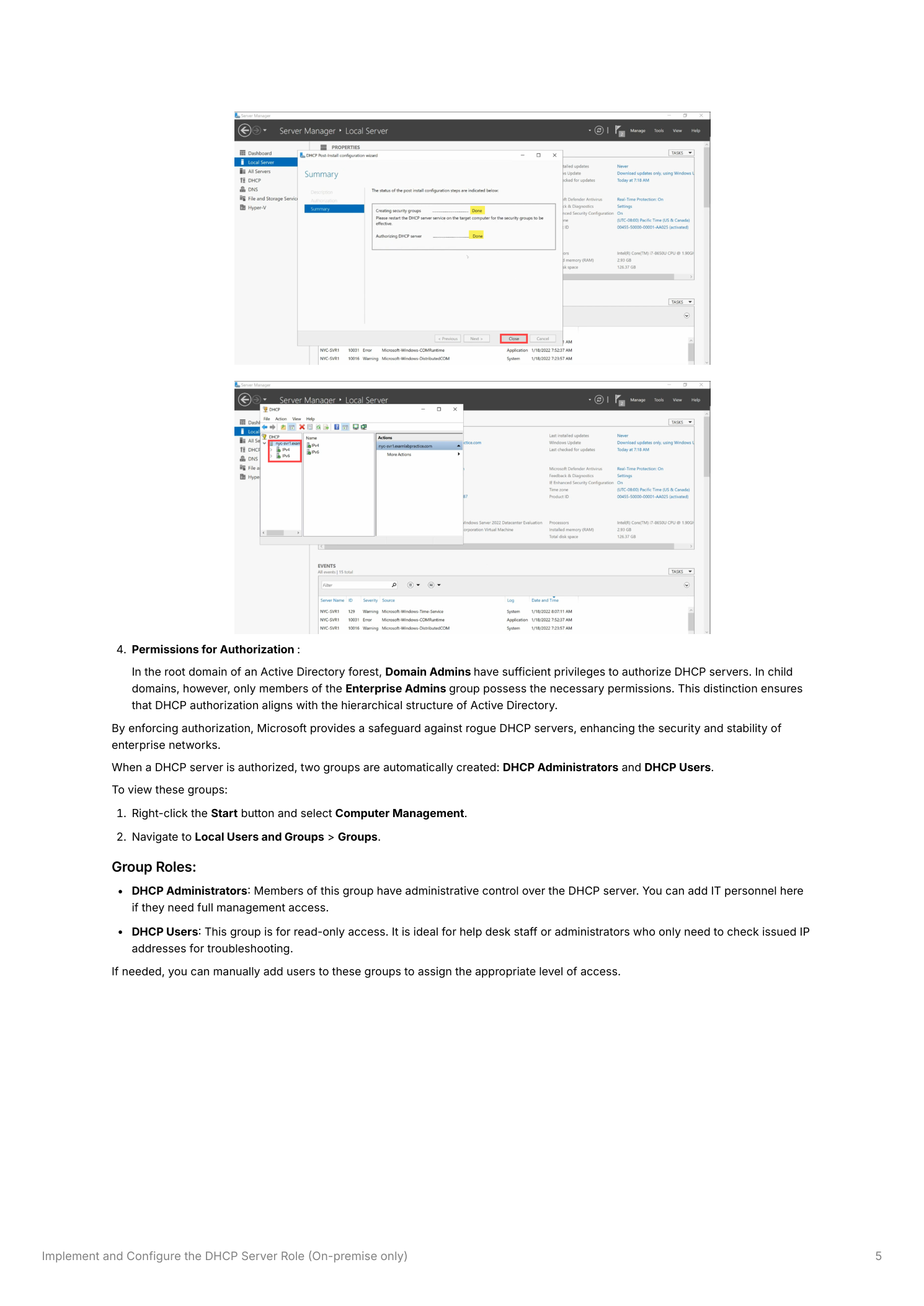
Step 4 – Complete the Post-Installation Wizard
The DHCP Post-Installation Configuration Wizard handles authorization automatically. In the wizard, specify the credentials to use for authorization (Domain Admin credentials are required in the root domain; Enterprise Admin credentials are required for child domains). The wizard will:
- Create two security groups in Active Directory: DHCP Administrators (full administrative control over DHCP) and DHCP Users (read-only access)
- Authorize the DHCP server in Active Directory
Click Commit to apply the configuration. The wizard will confirm successful completion.
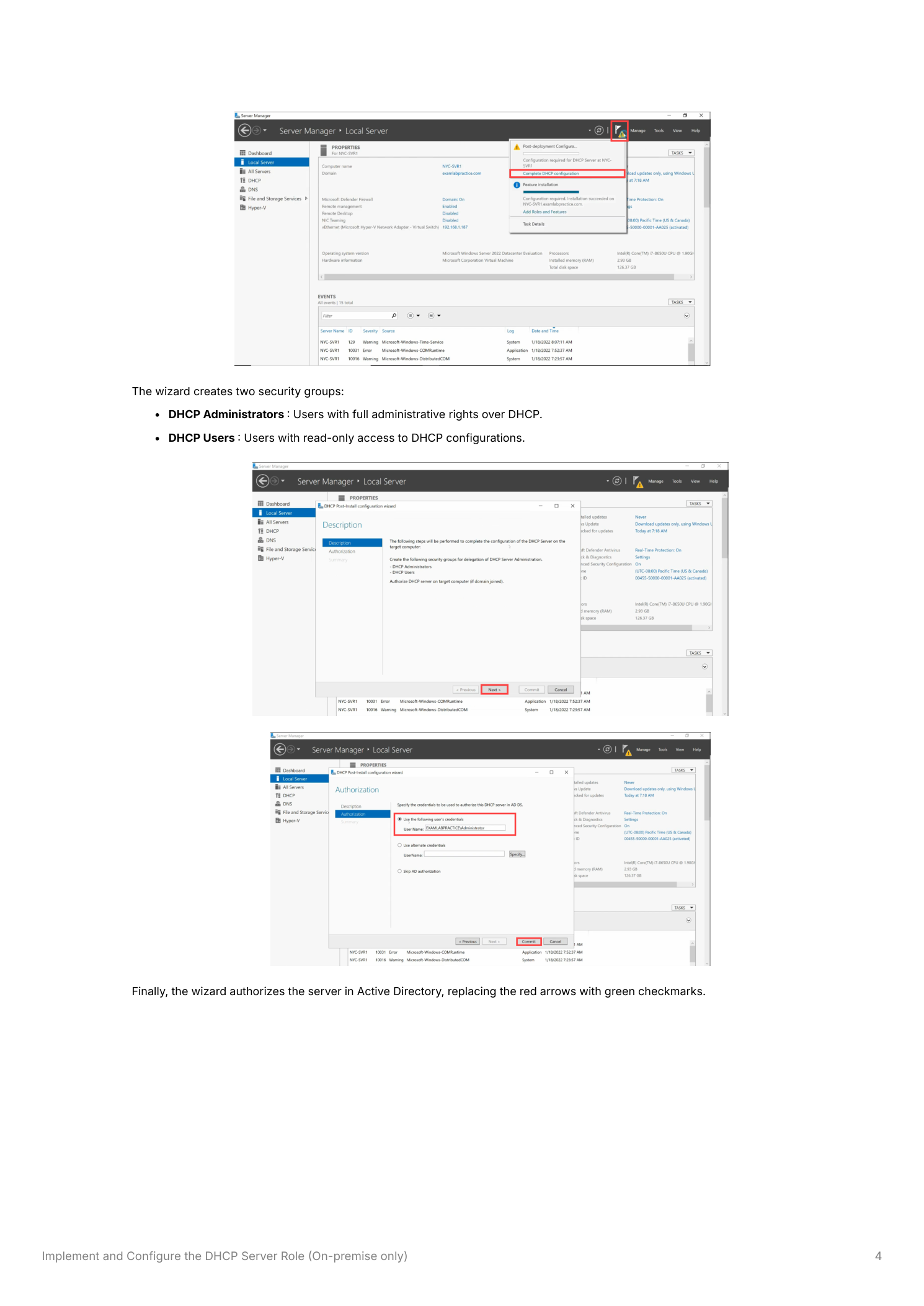
Step 5 – Verify Authorization
After the wizard completes, return to the DHCP console. The red arrows next to IPv4 and IPv6 should now be replaced with green upward arrows, confirming the server is authorized and ready to issue leases. In Server Manager, the warning notification should also clear.
Step 6 – Configure Scopes and Begin Issuing Addresses
With the DHCP server installed and authorized, the final step is to create a scope – the defined range of IP addresses that the server is allowed to assign. In the DHCP console, right-click IPv4 and select New Scope. The New Scope Wizard guides you through:
- Defining the Scope – Specify the start and end IP addresses, subnet mask, and any exclusions (IP ranges within the scope that should not be assigned – for example, addresses reserved for static devices). Configure the lease duration to determine how long a device retains its assigned address before needing to renew
- Assigning Network Parameters – Provide the default gateway and DNS server addresses that clients will receive along with their IP address
- Activating the Scope – Once configured, activate the scope to begin issuing addresses to clients
Understanding Authorization Permissions
DHCP authorization follows the Active Directory domain hierarchy:
- Root domain – Domain Admins have sufficient privileges to authorize DHCP servers. Any member of the Domain Admins group in the forest root domain can authorize DHCP servers across the entire forest
- Child domains – Only Enterprise Admins can authorize DHCP servers in child domains. Domain Admins of a child domain cannot authorize their own DHCP servers without Enterprise Admin involvement
This hierarchy ensures that DHCP authorization aligns with the trust structure of Active Directory, preventing local administrators in child domains from deploying unauthorized DHCP infrastructure.
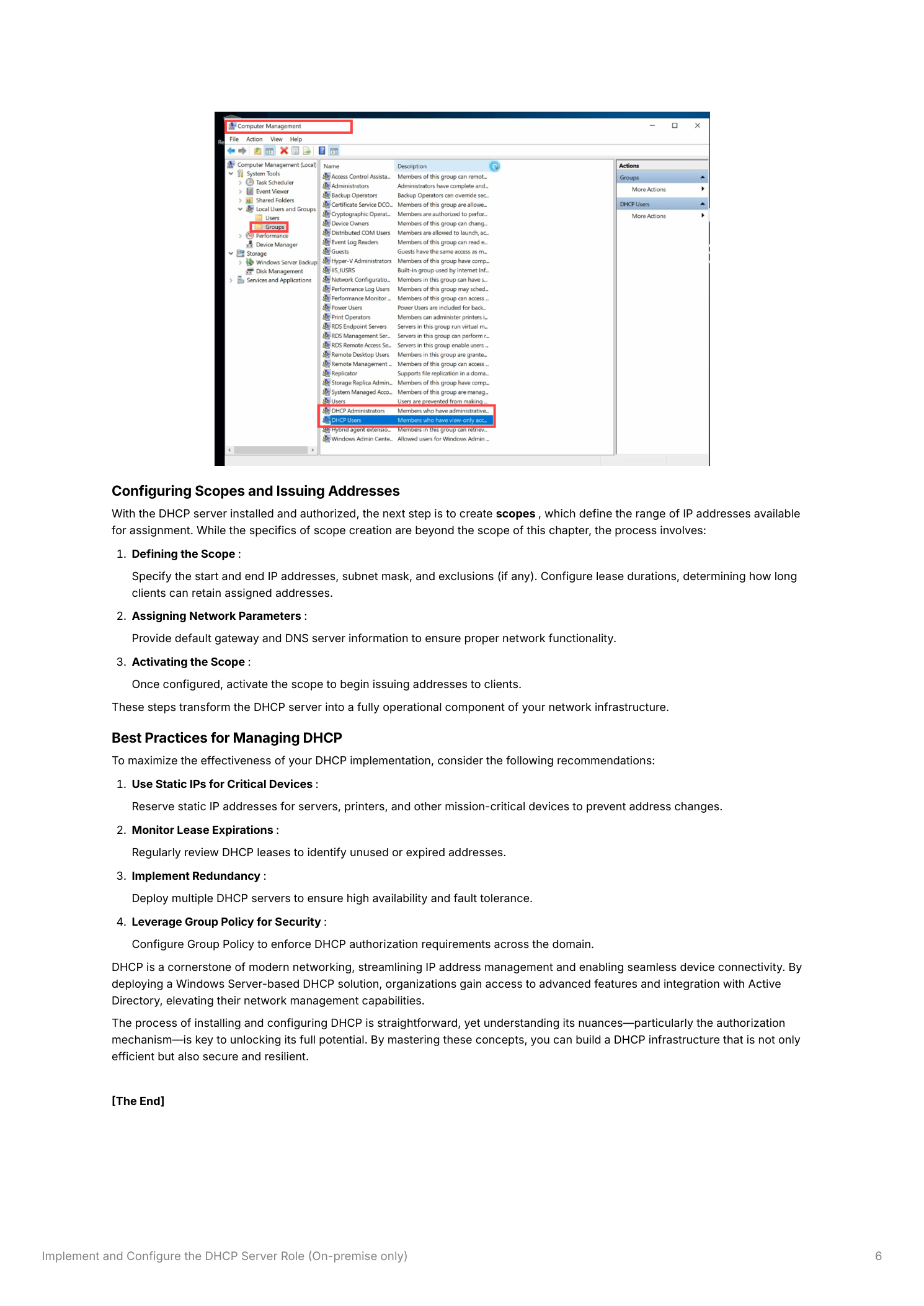
DHCP Security Groups
The two security groups created during authorization serve distinct purposes in delegated DHCP management:
- DHCP Administrators – Members have full administrative control over the DHCP server, including creating and modifying scopes, adding exclusions, configuring options, and viewing lease information. Add IT staff who need to manage DHCP to this group
- DHCP Users – Members have read-only access to DHCP configurations. This is ideal for help desk staff or administrators who need to look up IP assignments and lease information without the ability to make changes
To view and manage group membership, open Computer Management → Local Users and Groups → Groups and locate the DHCP Administrators and DHCP Users groups.
Best Practices
- Use Static IPs for Critical Devices – Reserve static addresses outside the DHCP scope for servers, printers, network devices, and other mission-critical infrastructure to prevent address changes after lease expiration
- Monitor Lease Utilization – Regularly review the DHCP console’s scope utilization view to identify scopes approaching exhaustion before clients begin experiencing failures
- Implement Redundancy – Deploy multiple DHCP servers with split scopes or DHCP failover to ensure high availability and fault tolerance – a single DHCP server failure can prevent all new clients from obtaining addresses
- Leverage Group Policy – Configure Group Policy to enforce DHCP authorization requirements across the domain, ensuring clients reject offers from unauthorized servers regardless of network location
