Overview
Active Directory auditing gives you full visibility into what’s happening in your domain — who created or modified accounts, what objects changed in the directory, and when audit policies themselves were altered. You configure it once through Group Policy and every domain controller picks up the settings automatically.
After applying the policy, run gpupdate /force on each domain controller or wait for the next replication cycle. Propagation time depends on your site topology and replication interval.
Prerequisites
- Windows Server 2008 R2 or later domain controllers
- Group Policy Management Console (GPMC) installed
- Domain Admin or equivalent permissions
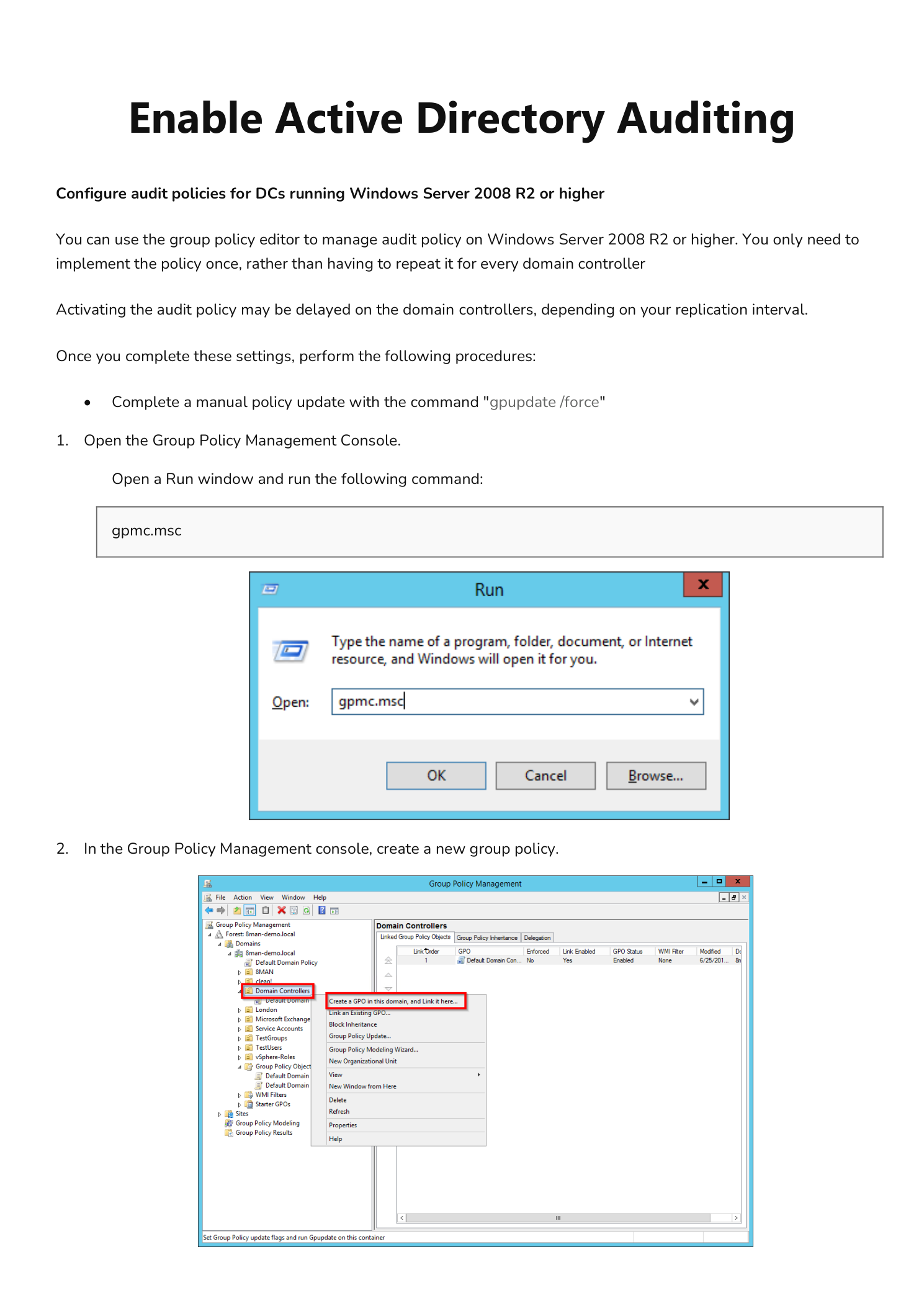
Step 1 — Open Group Policy Management Console
Open a Run dialog (Win + R), type gpmc.msc, and press OK.
Step 2 — Create a New Group Policy Object
In the Group Policy Management console, expand your domain, right-click the Domain Controllers container, and select Create a GPO in this domain, and Link it here. Give it a clear name such as AD Auditing Policy.
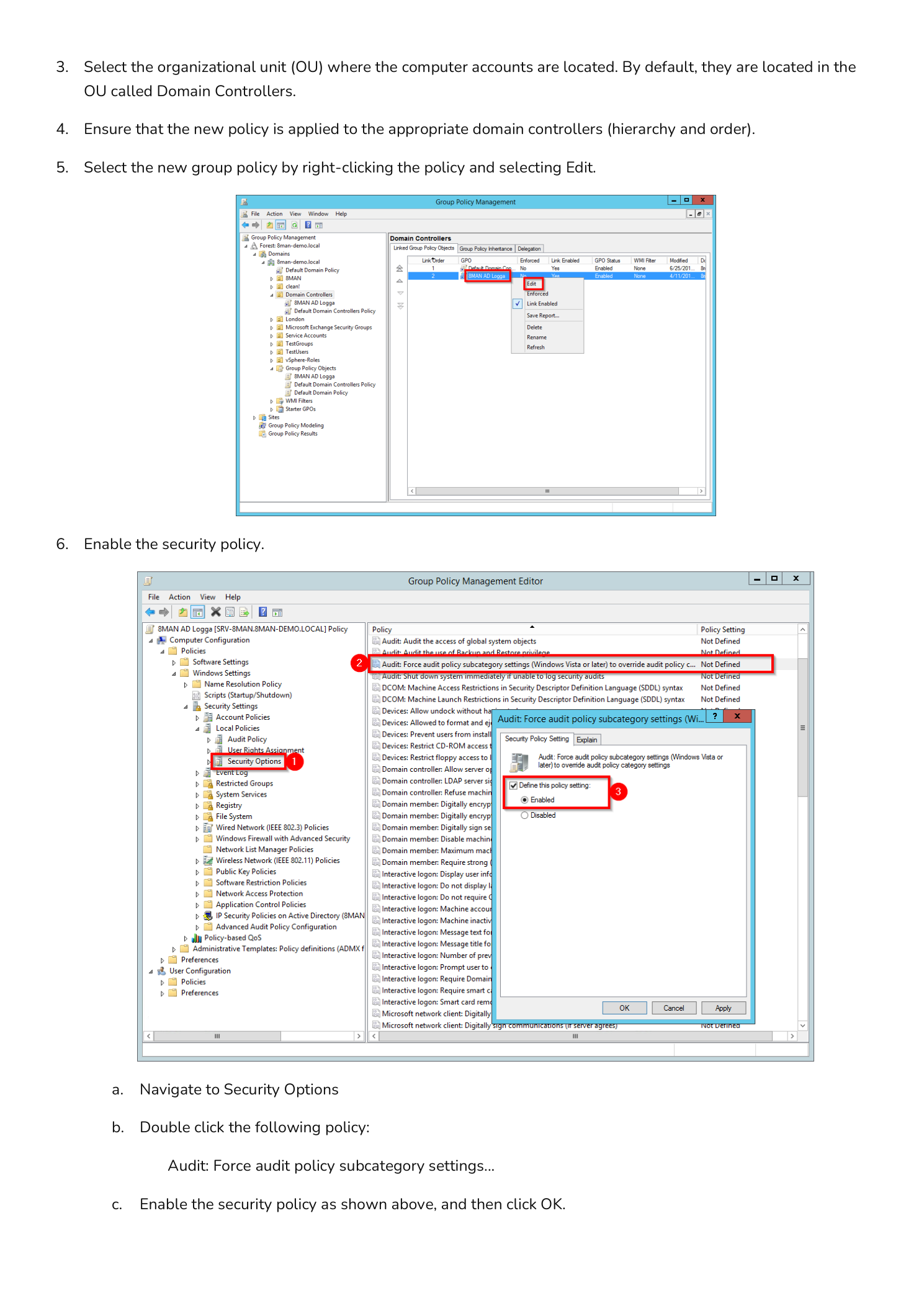
Step 3 — Confirm the OU and Apply Order
Select the OU where your domain controller computer accounts reside — by default Domain Controllers. If multiple GPOs are linked to that OU, confirm the link order so your new audit policy applies at the correct precedence.
Step 4 — Edit the GPO
Right-click the new policy and select Edit to open the Group Policy Management Editor.
Step 5 — Enable Force Audit Policy Subcategory Settings
Navigate to:
Computer Configuration > Windows Settings > Security Settings > Local Policies > Security OptionsDouble-click Audit: Force audit policy subcategory settings (Windows Vista or later) to override audit policy category settings. Set it to Enabled and click OK. This ensures granular subcategory settings take precedence over any legacy category-level audit policies.
Step 6 — Configure Account Management Auditing
Navigate to:
Computer Configuration > Windows Settings > Security Settings > Advanced Audit Policy Configuration > Audit Policies > Account ManagementSelect all subcategories using multi-select, right-click, and choose Properties. In the Properties for Multiple Items dialog, check Configure the following audit events and enable both Success and Failure. Click Apply, then OK.
Step 7 — Configure Audit Directory Service Changes
Navigate to DS Access under the same Advanced Audit Policy Configuration node. Double-click Audit Directory Service Changes, enable Configure the following audit events with both Success and Failure selected, click Apply, then OK.
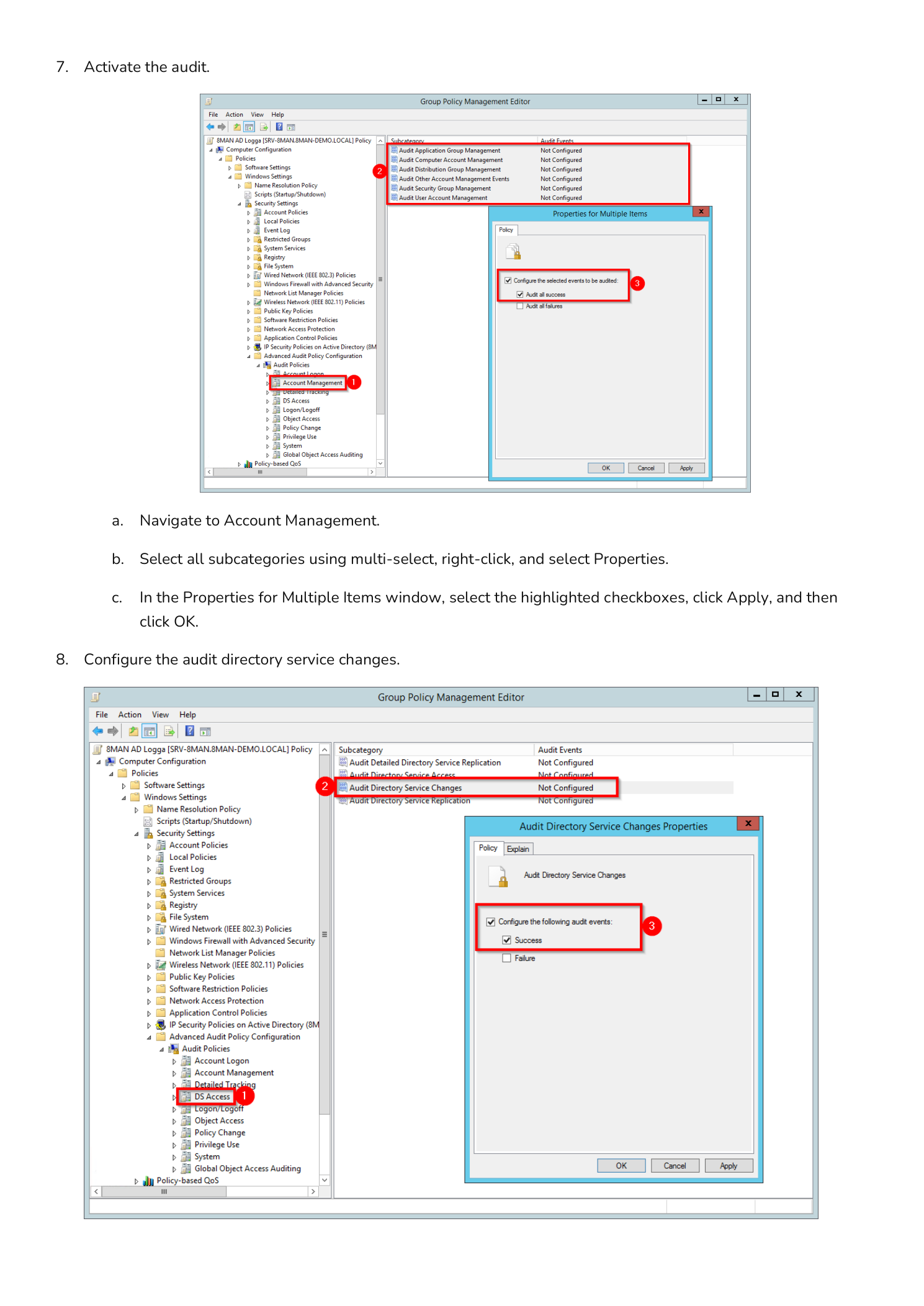
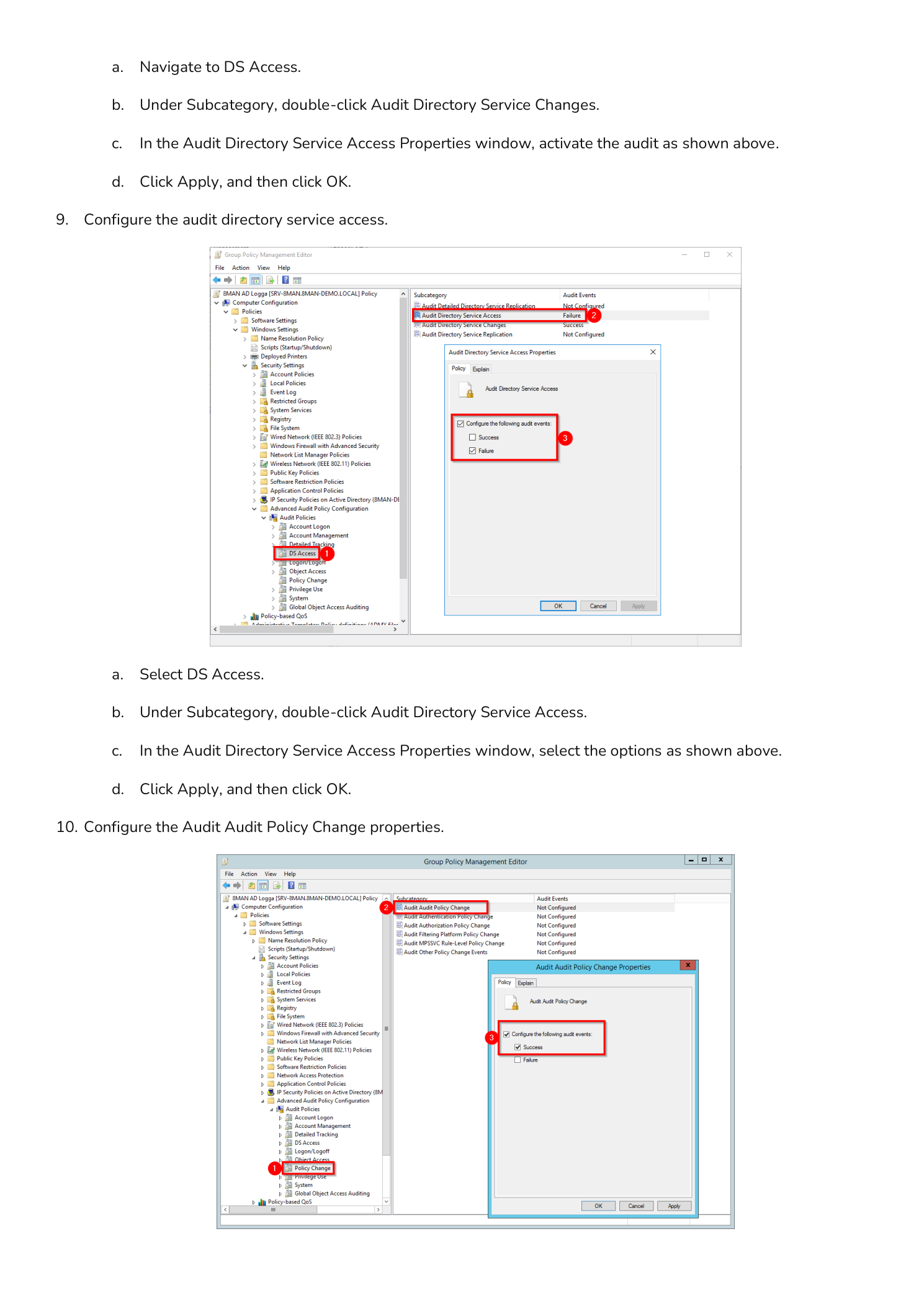
Step 8 — Configure Audit Directory Service Access
Still under DS Access, double-click Audit Directory Service Access. Enable Success and Failure auditing, click Apply, then OK.
Step 9 — Configure Audit Policy Change
Navigate to Policy Change under Advanced Audit Policy Configuration. Double-click Audit Audit Policy Change, enable Success and Failure, click Apply, then OK. This ensures any future changes to your audit settings are themselves logged.
Step 10 — Force a Group Policy Update
Open a Run dialog and execute the following command to immediately push the audit policy to the domain controller:
gpupdate /force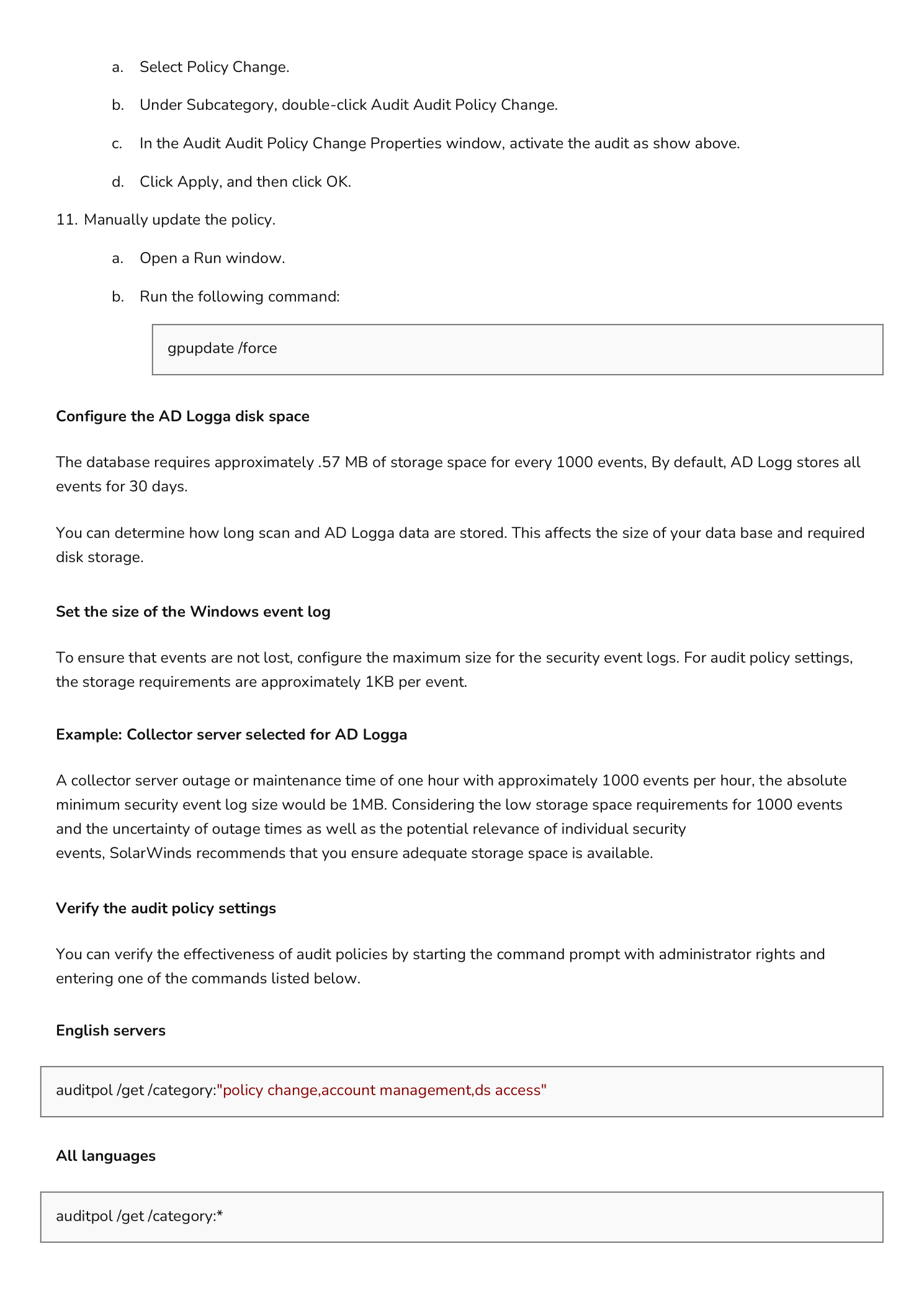
Storage Planning
AD Logga Disk Space
The audit database requires approximately 57 MB of storage per 1,000 events. By default, AD Logga retains events for 30 days. Plan your disk allocation based on expected event volume multiplied by your target retention period.
Windows Security Event Log Size
Configure the maximum size of the Security event log to prevent event loss during high-activity periods. Storage requirements are approximately 1 KB per event. For a collector server handling 1,000 events per hour with a one-hour maintenance window, the minimum recommended log size is 1 MB — scale accordingly for your environment.
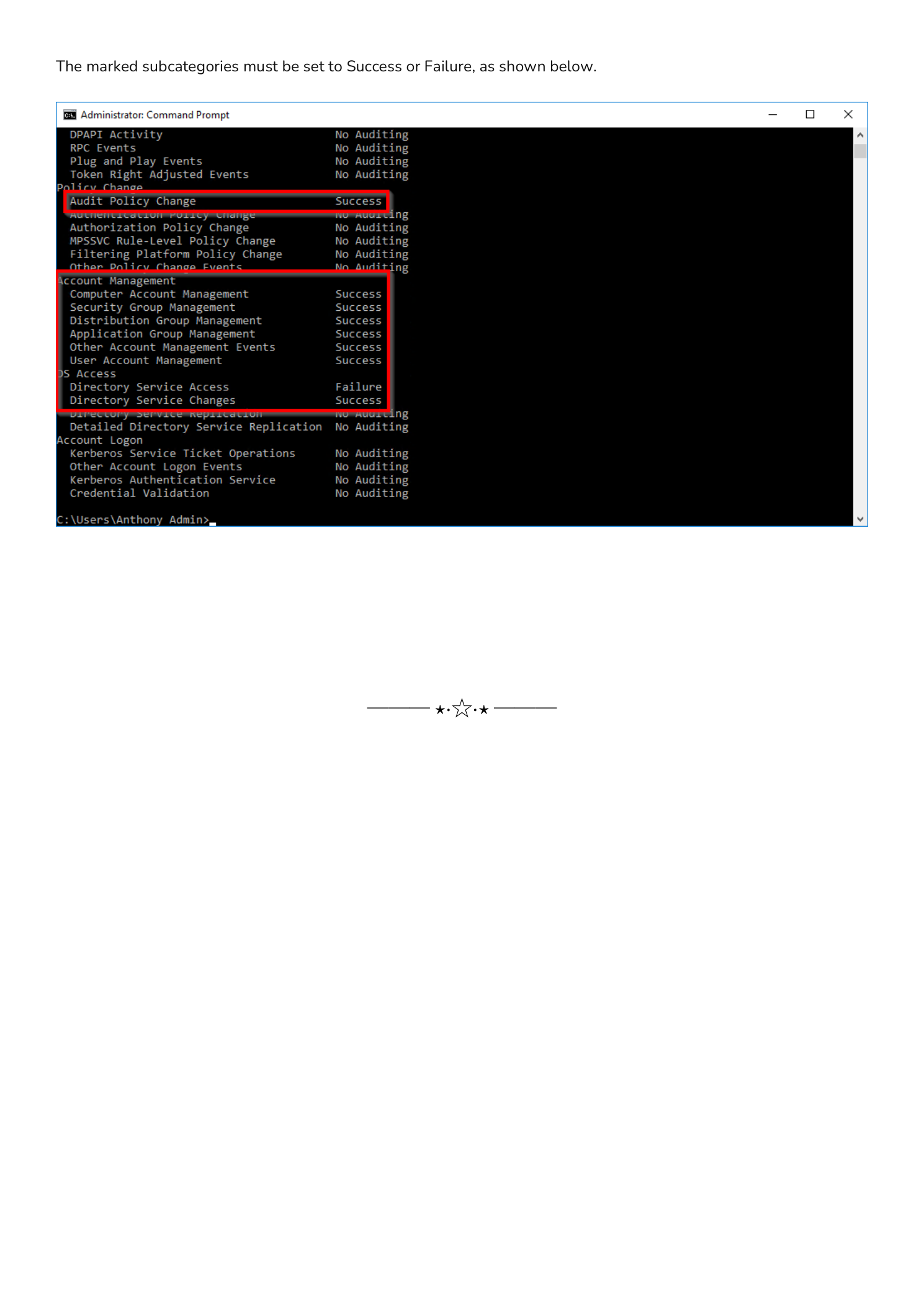
Verify the Audit Policy
Open an elevated Command Prompt and run one of the following commands to confirm audit subcategories are active:
Targeted check (English locale):
auditpol /get /category:"policy change,account management,ds access"Full policy dump (all locales):
auditpol /get /category:*The output should show each configured subcategory set to Success, Failure, or both — matching what you set in the GPO.