Overview
Trust relationships between AD domains allow users in one domain to authenticate to resources in another. They are most commonly configured when merging or migrating multiple organizations. In this guide we establish a two-way forest trust between two independent Active Directory forests – contoso.loc and test.loc.
Trust relationships can only be configured between Active Directory forest root domains. Before creating the trust, both sides must be able to resolve each other’s DNS names, which requires conditional forwarding on each domain’s DNS servers.
Prerequisites
- Two independent Active Directory forests with at least one domain controller each
- Enterprise Admin credentials in both forests
- Network connectivity between domain controllers in both forests
Part 1 – Configure DNS Conditional Forwarding
Each forest’s DNS servers must be able to resolve names in the other forest before the trust wizard will succeed.
Step 1 – Open DNS Manager in contoso.loc
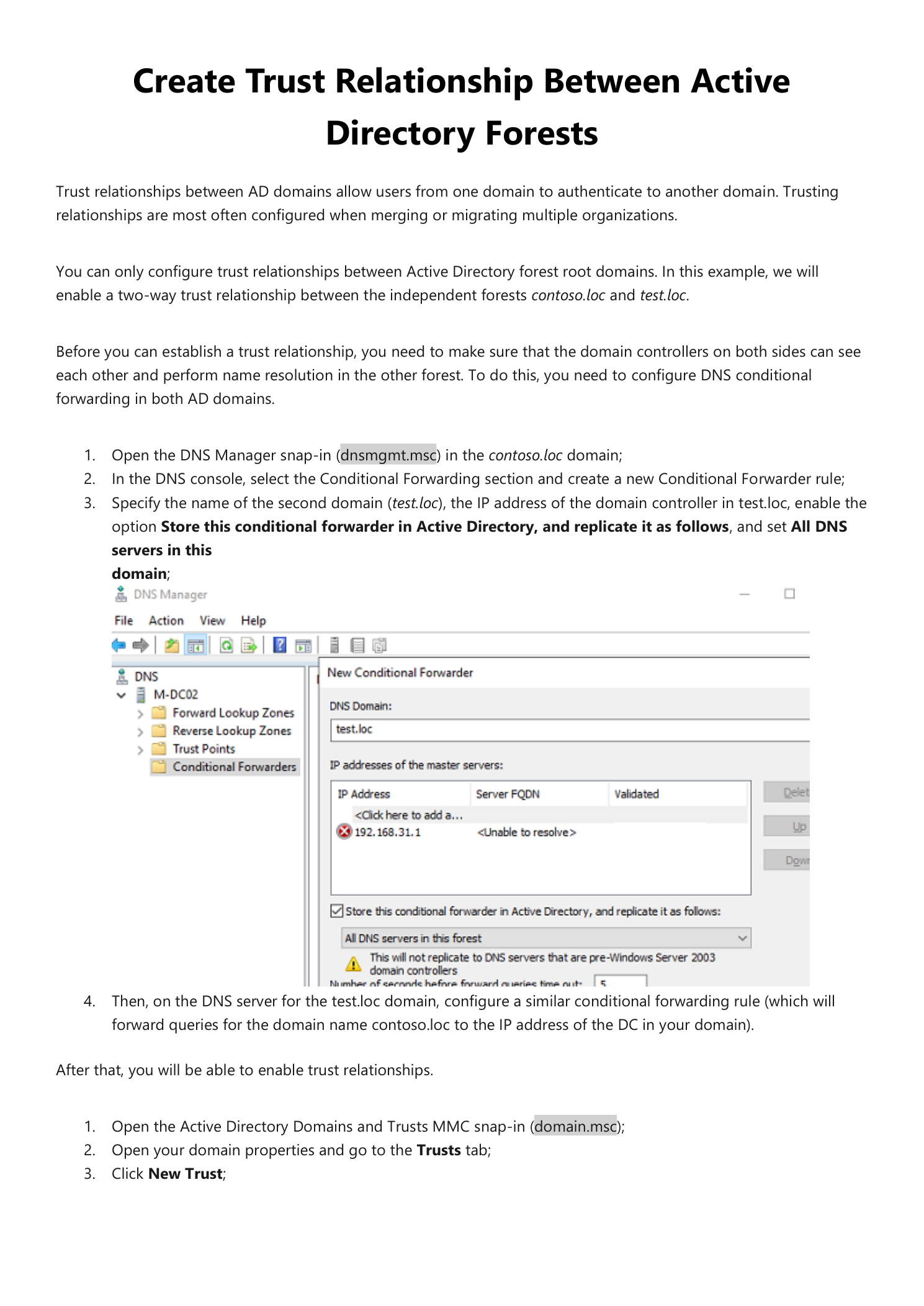
On a domain controller in contoso.loc, open a Run dialog (Win + R), type dnsmgmt.msc, and press OK.
Step 2 – Create a Conditional Forwarder for test.loc
In the DNS Manager console, expand your server, right-click Conditional Forwarders, and select New Conditional Forwarder. Configure the following:
- DNS Domain:
test.loc - IP addresses of master servers: IP address of the domain controller in test.loc
- Check Store this conditional forwarder in Active Directory, and replicate it as follows and select All DNS servers in this domain
Click OK to save.
Step 3 – Mirror the Conditional Forwarder in test.loc
Repeat the same process on a domain controller in test.loc. Create a conditional forwarder for contoso.loc pointing to the IP address of the contoso.loc domain controller. Store it in Active Directory and replicate to all DNS servers in the test.loc domain.
Part 2 – Create the Trust Relationship
Step 4 – Open Active Directory Domains and Trusts
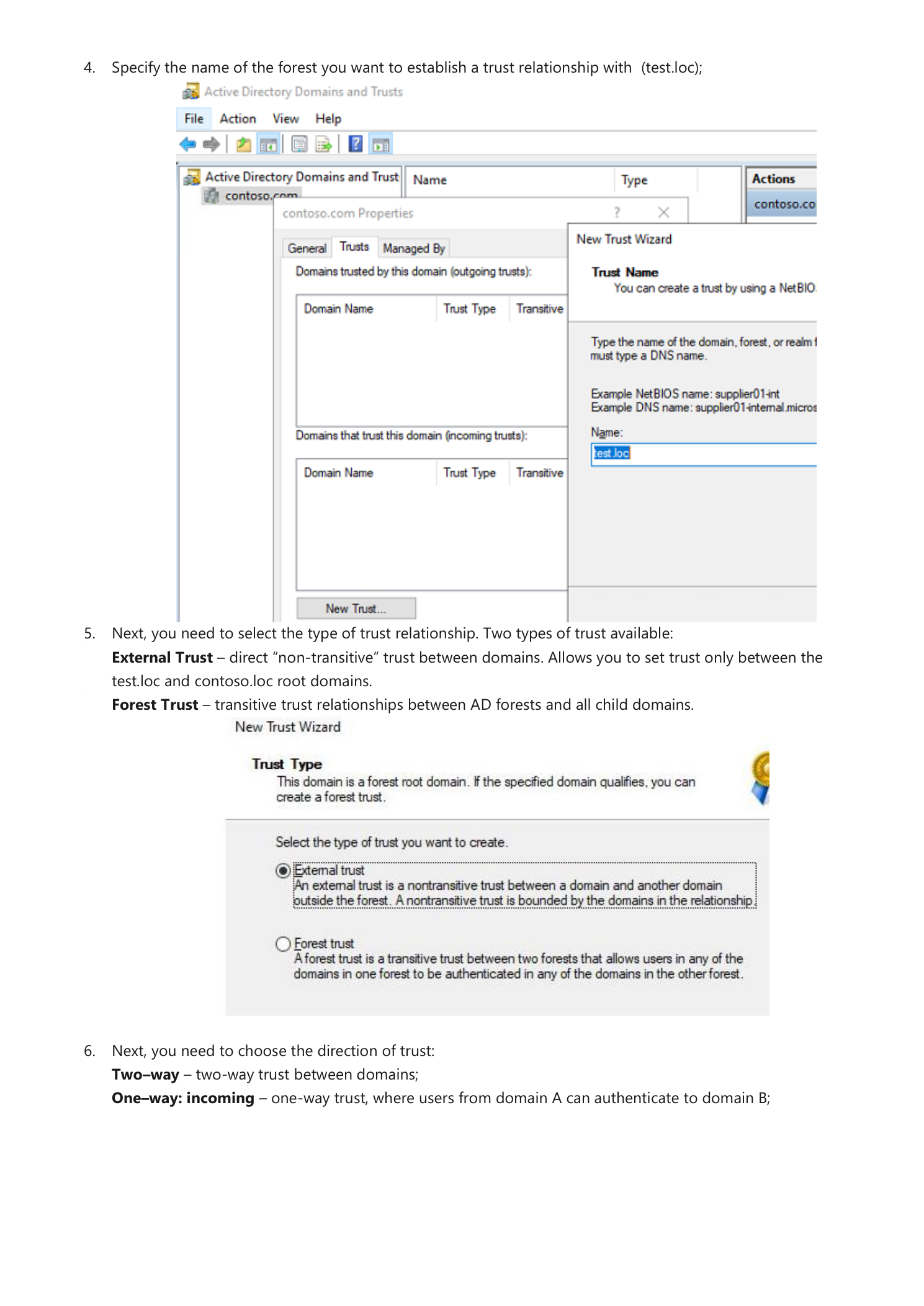
On a domain controller in contoso.loc, open a Run dialog and type domain.msc. In the console, right-click your domain (contoso.loc) and select Properties. Navigate to the Trusts tab and click New Trust.
Step 5 – Enter the Forest Name
In the New Trust Wizard, type the name of the forest you want to trust – in this example test.loc – in the Name field and click Next.
Step 6 – Select the Trust Type
Choose the type of trust to create:
- External Trust – a non-transitive trust between this domain and one other domain, bounded by the domains in the relationship
- Forest Trust – a transitive trust between two complete AD forests and all their child domains; users in any domain in either forest can authenticate across the trust
Select Forest Trust and click Next.
Step 7 – Choose the Trust Direction
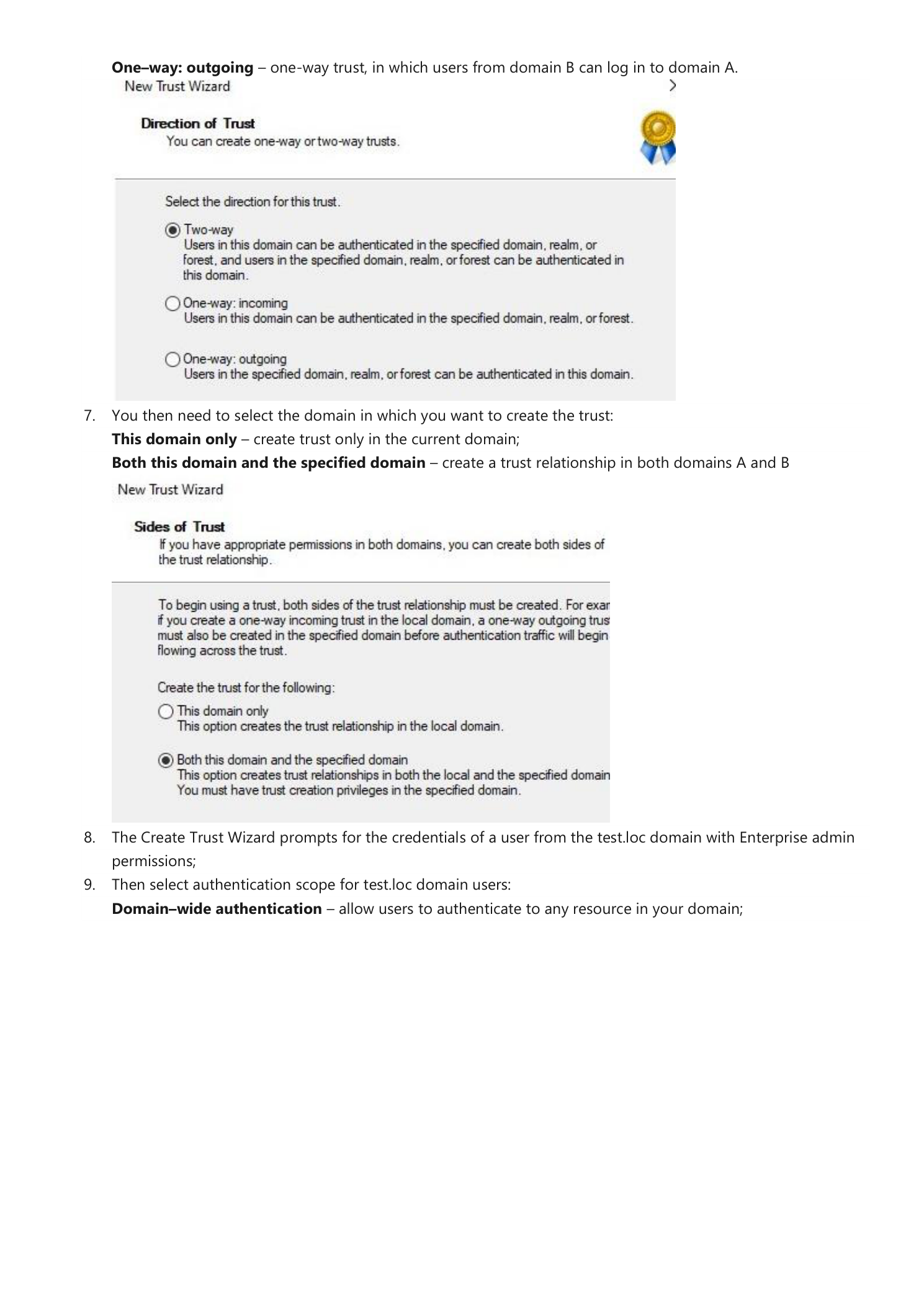
Select the direction of authentication:
- Two-way – users in either domain can authenticate in the other domain, realm, or forest
- One-way: incoming – users in this domain can authenticate in the specified domain or forest
- One-way: outgoing – users in the specified domain or forest can authenticate in this domain
Select Two-way and click Next.
Step 8 – Select the Sides of Trust
Choose where to create the trust relationship:
- This domain only – creates the trust object only in the current domain; you must create the matching trust in the other domain separately
- Both this domain and the specified domain – creates trust objects in both forests simultaneously, requiring Enterprise Admin credentials for both
Select Both this domain and the specified domain and click Next.
Step 9 – Enter Enterprise Admin Credentials for test.loc
The wizard prompts for the credentials of a user in test.loc with Enterprise Admin permissions. Enter these credentials to allow the wizard to create the trust object in the remote forest.
Step 10 – Select the Authentication Scope
Choose how users from test.loc will authenticate to resources in contoso.loc:
- Domain-wide authentication – Windows automatically authenticates users from test.loc to any resource in the local domain. Use this when both forests belong to the same organization.
- Selective authentication – Windows does not automatically authenticate users from test.loc. Instead, you manually grant individual access to specific servers in contoso.loc. Use this for cross-organization trusts where you want granular access control.
Click Next through the remaining wizard pages to create the trust.
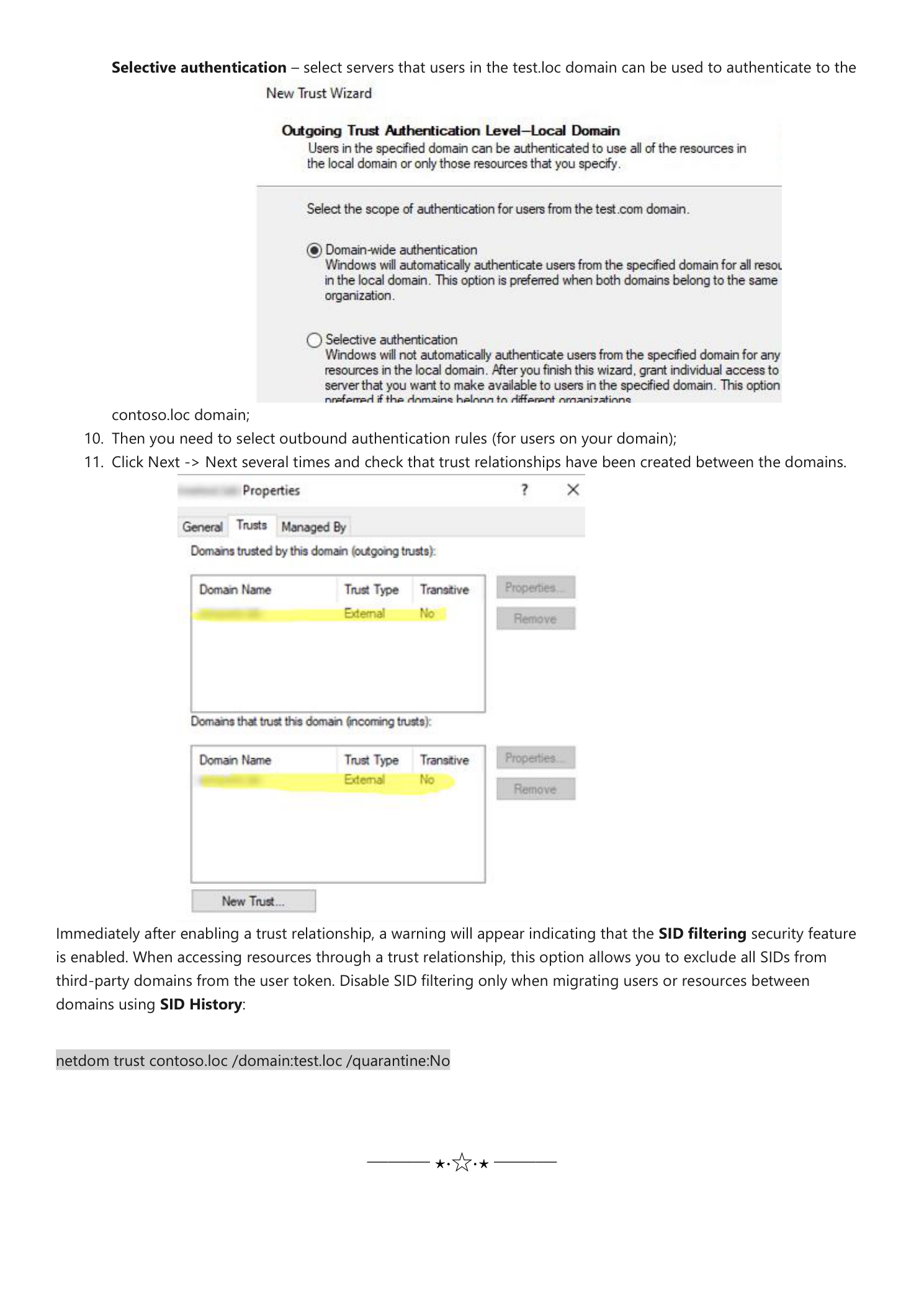
Disable SID Filtering (Migration Scenarios Only)
When you access resources through a trust relationship, Windows enables SID filtering by default. This excludes all SIDs from third-party domains from the user token, protecting against privilege escalation via SID History.
If you are migrating users or resources between domains using SID History, you will need to disable SID filtering for the trust. Run the following on a domain controller in contoso.loc:
netdom trust contoso.loc /domain:test.loc /quarantine:NoOnly disable SID filtering when performing an active migration. Re-enable it once the migration is complete to restore the security boundary.
