Overview
Accidentally deleting an Active Directory object – a user account, security group, or computer – is one of the most common administrative mistakes in an AD environment. If the Active Directory Recycle Bin is enabled, deleted objects are retained with all their attributes intact for the duration of the tombstone lifetime (180 days by default), giving administrators a straightforward recovery path before the object is permanently removed by garbage collection.
This guide explains how the AD object lifecycle works with and without the Recycle Bin, and walks through restoring a deleted object using the Active Directory Administrative Center (ADAC) – the graphical tool available from Windows Server 2012 onwards.
Prerequisites
- Active Directory Recycle Bin enabled on the domain (requires Windows Server 2008 R2 forest functional level or higher)
- Windows Server 2012 or later for the ADAC graphical method
- Domain Admin permissions
- The deleted object must still be within the tombstone lifetime – objects older than the configured lifetime have already been permanently removed by the garbage collector
Part 1 – Understanding the Object Lifecycle
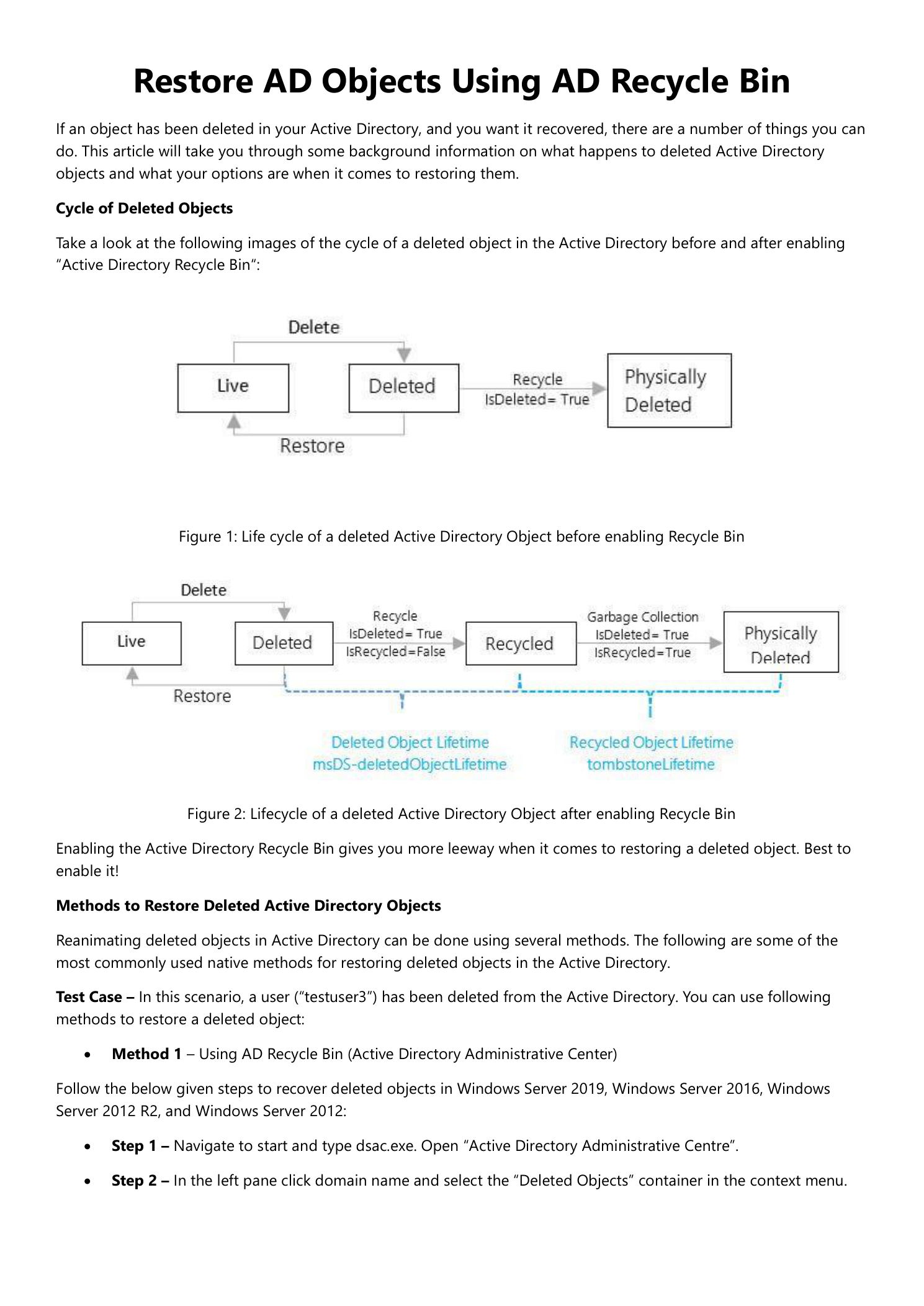
Before restoring a deleted object, it helps to understand what actually happens when an object is deleted in Active Directory, and how enabling the Recycle Bin changes that lifecycle.
Without the AD Recycle Bin
When an object is deleted, AD marks it as deleted (isDeleted = True) and strips most of its attributes, retaining only a minimal set. The object moves to the Deleted Objects container. During this phase it can technically be reanimated using low-level tools, but most of its original attributes – group memberships, passwords, profile paths – are already gone. After the tombstone lifetime expires, the garbage collector removes it permanently.
With the AD Recycle Bin Enabled
The Recycle Bin adds an additional phase to the lifecycle. When an object is deleted, it first enters a logically deleted state (isDeleted = True, isRecycled = False) for the duration of the deleted object lifetime (msDS-deletedObjectLifetime). All original attributes are preserved. After that window, it transitions to a recycled state (isRecycled = True) for the tombstone lifetime before being permanently destroyed.
The key advantage: objects in the logically deleted phase can be fully restored – including group memberships, passwords, and all other attributes – with a single restore operation.
Part 2 – Restore Using Active Directory Administrative Center
The Active Directory Administrative Center (ADAC) provides a graphical interface for browsing and restoring objects from the Deleted Objects container. This method is available on Windows Server 2012 and later.
Step 1 – Open Active Directory Administrative Center
In Server Manager, go to Tools and select Active Directory Administrative Center. Alternatively, run dsac.exe from the Start menu or Run dialog.
Step 2 – Navigate to the Deleted Objects Container
In the left navigation pane, click your domain name. Right-click the domain node and select Deleted Objects from the context menu. The Deleted Objects container opens, showing all objects currently in the AD Recycle Bin.
Step 3 – Restore the Deleted Object
Locate the object you want to restore. You can use the Filter bar to search by name. Once you find the object, right-click it and select Restore – or select it and click Restore in the Tasks panel on the right. To restore the object to a different OU than its original location, use Restore To instead.
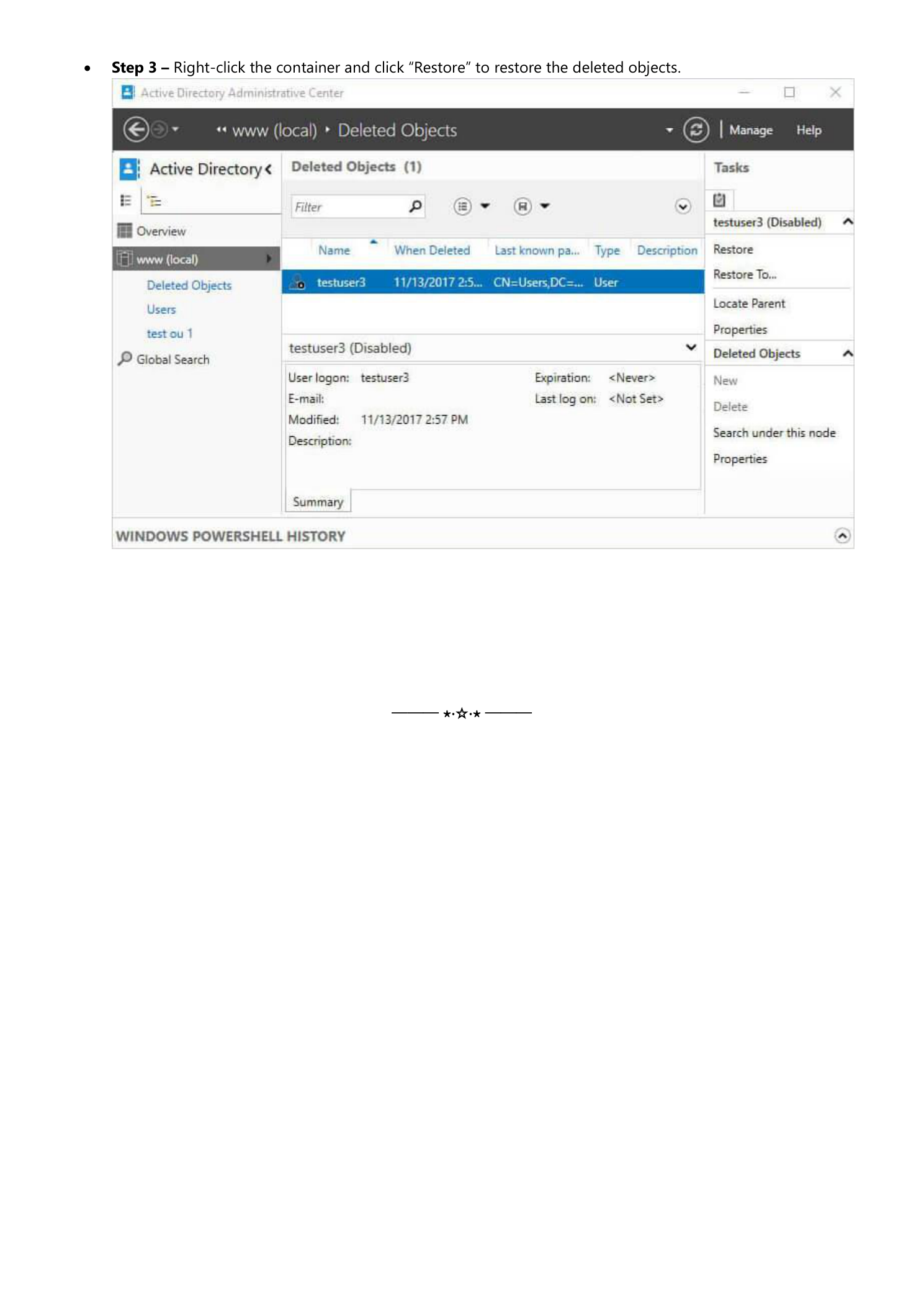
After clicking Restore, refresh the Deleted Objects container – the object will no longer appear there. Navigate to the OU where the account originally lived to confirm it has been returned. The restored object will initially show as disabled; re-enable it and reset the password if needed before returning it to the user.
Part 3 – Restore via PowerShell
For environments running Windows Server 2008 R2, or for scripted / bulk restore operations, use the Active Directory PowerShell module. First find the deleted object, then restore it:
# Find the deleted object
Get-ADObject -Filter {isDeleted -eq True -and Name -like "*testuser3*"}
-IncludeDeletedObjects | Format-List DistinguishedName, Name, ObjectGUID
# Restore it to its original location
Get-ADObject -Filter {isDeleted -eq True -and samaccountname -eq "testuser3"}
-IncludeDeletedObjects | Restore-ADObjectTo restore to a specific OU rather than the original location, add the -TargetPath parameter:
Restore-ADObject -Identity "<ObjectGUID>" -TargetPath "OU=Users,DC=domain,DC=com"Important Considerations
Enable the Recycle Bin Before You Need It
The AD Recycle Bin must be enabled before objects are deleted to provide full attribute preservation. Enabling it retroactively does not protect objects that were already deleted. Enable it as part of your standard AD forest setup: Active Directory Administrative Center → right-click domain → Enable Recycle Bin. This operation cannot be reversed.
Tombstone Lifetime vs. Deleted Object Lifetime
The default deleted object lifetime is 180 days. After this window the object transitions to the recycled state, where most attributes are stripped and the object can no longer be fully restored. Check your environment’s configured lifetime with: (Get-ADObject -Identity "CN=Directory Service,CN=Windows NT,CN=Services,CN=Configuration,DC=domain,DC=com" -Properties msDS-DeletedObjectLifetime).'msDS-DeletedObjectLifetime'
Re-enable and Reset the Restored Account
Objects restored from the Recycle Bin are typically in a disabled state. After restoring, navigate to the account in Active Directory Users and Computers (or ADAC), re-enable it, and issue a temporary password. Group memberships and all other attributes are fully restored, so the account should be functional immediately after re-enabling.
